Intro
Explore Cyber Security Specialties, including threat analysis, penetration testing, and incident response, to protect against cyber threats and vulnerabilities with expert security measures and solutions.
The world of cyber security is vast and complex, with a wide range of specialties that cater to different aspects of protecting digital information and systems. As technology advances and new threats emerge, the demand for skilled cyber security professionals has never been higher. In this article, we will delve into the various cyber security specialties, exploring their roles, responsibilities, and the skills required to succeed in these fields.
Cyber security is a critical component of modern business, and its importance cannot be overstated. With the increasing reliance on digital technologies, organizations are vulnerable to a wide range of cyber threats, from malware and phishing attacks to denial-of-service (DoS) and ransomware attacks. Cyber security specialists play a crucial role in protecting against these threats, using their expertise to design, implement, and maintain secure systems and networks.
The field of cyber security is constantly evolving, with new specialties emerging as technology advances. Some of the most in-demand cyber security specialties include penetration testing, incident response, security consulting, and cloud security. These specialties require a deep understanding of cyber security principles, as well as the ability to stay up-to-date with the latest threats and technologies.
Cyber Security Specialties Overview
Cyber security specialties can be broadly categorized into several key areas, including security management, security architecture, security engineering, and security operations. Security management involves overseeing the overall cyber security strategy and direction of an organization, while security architecture focuses on designing and implementing secure systems and networks. Security engineering involves developing and testing secure software and hardware, and security operations involves monitoring and responding to cyber security incidents.
Security Management
Security management is a critical cyber security specialty that involves overseeing the overall cyber security strategy and direction of an organization. Security managers are responsible for developing and implementing cyber security policies, procedures, and standards, as well as ensuring compliance with regulatory requirements. They must also stay up-to-date with the latest cyber security threats and trends, and be able to communicate effectively with stakeholders at all levels of the organization.Security Architecture
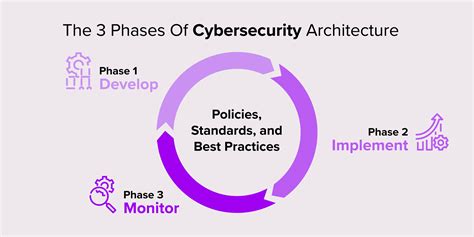
Security architecture is a cyber security specialty that involves designing and implementing secure systems and networks. Security architects must have a deep understanding of cyber security principles, as well as the ability to design and implement secure systems and networks. They must also be able to conduct risk assessments and vulnerability testing, and develop strategies for mitigating cyber security threats.
Security Engineering
Security engineering is a cyber security specialty that involves developing and testing secure software and hardware. Security engineers must have a strong background in computer science and engineering, as well as a deep understanding of cyber security principles. They must be able to design and develop secure software and hardware, as well as test and evaluate the security of existing systems and networks.Security Operations
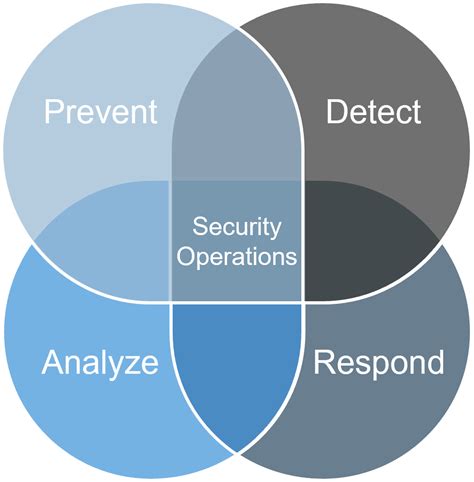
Security operations is a cyber security specialty that involves monitoring and responding to cyber security incidents. Security operations specialists must have a deep understanding of cyber security principles, as well as the ability to monitor and analyze security event logs. They must also be able to respond quickly and effectively to cyber security incidents, and develop strategies for preventing future incidents.
Incident Response
Incident response is a critical cyber security specialty that involves responding to and managing cyber security incidents. Incident response specialists must have a deep understanding of cyber security principles, as well as the ability to respond quickly and effectively to cyber security incidents. They must also be able to develop strategies for preventing future incidents, and communicate effectively with stakeholders at all levels of the organization.Penetration Testing

Penetration testing is a cyber security specialty that involves simulating cyber attacks on an organization's systems and networks. Penetration testers must have a deep understanding of cyber security principles, as well as the ability to use a range of tools and techniques to simulate cyber attacks. They must also be able to identify vulnerabilities and develop strategies for mitigating them.
Cloud Security
Cloud security is a cyber security specialty that involves protecting cloud-based systems and data. Cloud security specialists must have a deep understanding of cloud computing principles, as well as the ability to design and implement secure cloud-based systems and networks. They must also be able to conduct risk assessments and vulnerability testing, and develop strategies for mitigating cyber security threats in the cloud.Cyber Security Career Paths

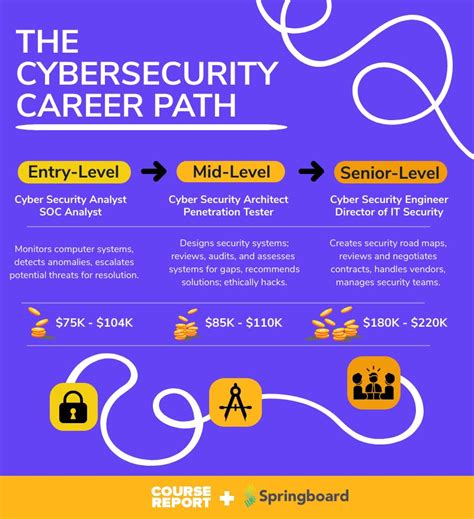
Cyber security career paths can vary widely, depending on the individual's interests, skills, and experience. Some common cyber security career paths include security analyst, security consultant, penetration tester, and chief information security officer (CISO). Security analysts are responsible for monitoring and analyzing security event logs, while security consultants work with organizations to develop and implement cyber security strategies. Penetration testers simulate cyber attacks on an organization's systems and networks, and CISOs oversee the overall cyber security strategy and direction of an organization.
Cyber Security Education and Training
Cyber security education and training are critical for individuals looking to pursue a career in cyber security. There are a range of cyber security courses and certifications available, including CompTIA Security+, Certified Information Systems Security Professional (CISSP), and Certified Ethical Hacker (CEH). These courses and certifications can provide individuals with the knowledge and skills they need to succeed in the field of cyber security.Cyber Security Industry Trends

The cyber security industry is constantly evolving, with new trends and technologies emerging all the time. Some of the current trends in the cyber security industry include the use of artificial intelligence (AI) and machine learning (ML) to detect and respond to cyber threats, the increasing importance of cloud security, and the growing demand for cyber security professionals with expertise in areas such as penetration testing and incident response.
Cyber Security Challenges
Cyber security challenges are numerous and varied, and can include everything from phishing and ransomware attacks to denial-of-service (DoS) and SQL injection attacks. To address these challenges, organizations must have a comprehensive cyber security strategy in place, as well as the right tools and technologies to detect and respond to cyber threats. They must also have a team of skilled cyber security professionals who can develop and implement cyber security policies, procedures, and standards.Cyber Security Best Practices

Cyber security best practices can help organizations protect against cyber threats and minimize the risk of a cyber security breach. Some of the most effective cyber security best practices include implementing a comprehensive cyber security strategy, conducting regular risk assessments and vulnerability testing, and providing ongoing cyber security education and training to employees. Organizations should also have a incident response plan in place, and conduct regular security audits and penetration testing.
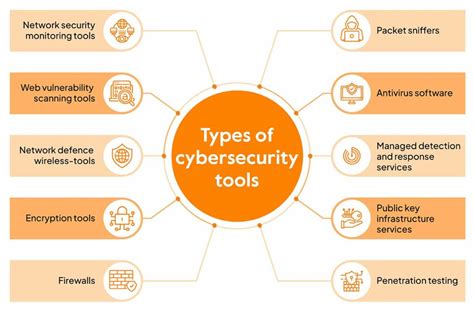
Cyber Security Tools and Technologies
Cyber security tools and technologies are essential for detecting and responding to cyber threats. Some of the most common cyber security tools and technologies include firewalls, intrusion detection systems (IDS), and antivirus software. Organizations should also consider using advanced threat protection (ATP) tools, such as sandboxing and threat intelligence platforms, to detect and respond to sophisticated cyber threats.Cyber Security Image Gallery








What is cyber security?
+Cyber security refers to the practices, technologies, and processes designed to protect digital information, systems, and networks from unauthorized access, use, disclosure, disruption, modification, or destruction.
Why is cyber security important?
+Cyber security is important because it helps protect against cyber threats, which can have serious consequences for individuals, organizations, and society as a whole.
What are some common cyber security threats?
+Some common cyber security threats include phishing, ransomware, denial-of-service (DoS) attacks, and SQL injection attacks.
How can I protect myself from cyber threats?
+You can protect yourself from cyber threats by using strong passwords, keeping your software up-to-date, being cautious when clicking on links or opening attachments, and using antivirus software.
What is the future of cyber security?
+The future of cyber security is likely to involve the use of artificial intelligence (AI) and machine learning (ML) to detect and respond to cyber threats, as well as the increasing importance of cloud security and the growing demand for cyber security professionals with expertise in areas such as penetration testing and incident response.
In conclusion, cyber security is a critical component of modern business, and its importance cannot be overstated. With the increasing reliance on digital technologies, organizations are vulnerable to a wide range of cyber threats, from malware and phishing attacks to denial-of-service (DoS) and ransomware attacks. By understanding the various cyber security specialties, staying up-to-date with the latest trends and technologies, and implementing effective cyber security strategies, organizations can protect themselves from cyber threats and minimize the risk of a cyber security breach. We invite you to share your thoughts and experiences on cyber security in the comments below, and to share this article with others who may be interested in learning more about this critical topic.
