Intro
Discover Anti Access Area Denial strategies, including maritime denial and counter-A2AD tactics, to restrict adversary movement and gain battlefield advantage in modern warfare.
The concept of Anti-Access Area Denial (A2AD) strategies has become increasingly important in modern warfare, as nations seek to protect their sovereignty and territorial integrity from potential threats. A2AD strategies refer to the use of military capabilities to prevent or restrict an adversary's ability to access or operate within a specific area or region. This can include a range of tactics, such as missile defense systems, air defense systems, and naval blockade. In this article, we will explore the importance of A2AD strategies, their benefits, and the various ways in which they can be implemented.
A2AD strategies are crucial in today's security environment, where the threat of military intervention or invasion is ever-present. By denying an adversary access to a specific area or region, a nation can protect its vital interests, such as its capital city, major population centers, or strategic military installations. A2AD strategies can also be used to prevent an adversary from using a particular area as a staging ground for military operations, thereby limiting their ability to project power. Furthermore, A2AD strategies can be used to defend against a range of threats, including ballistic missiles, cruise missiles, and cyber attacks.
The benefits of A2AD strategies are numerous. For one, they can provide a nation with a significant military advantage, allowing it to deter or defeat an adversary without having to engage in direct combat. A2AD strategies can also help to reduce the risk of military escalation, by limiting the ability of an adversary to launch a surprise attack. Additionally, A2AD strategies can be used to protect a nation's economic interests, such as its trade routes or natural resources. By denying an adversary access to these areas, a nation can prevent them from disrupting its economy or exploiting its resources.
Understanding A2AD Strategies
To understand A2AD strategies, it is essential to consider the various components that make up these systems. These components can include missile defense systems, air defense systems, naval blockade, and cyber warfare capabilities. Missile defense systems, such as the Patriot or THAAD systems, are designed to detect and intercept incoming ballistic missiles, preventing them from reaching their target. Air defense systems, such as the S-400 or F-35, are designed to detect and intercept incoming aircraft, preventing them from entering a nation's airspace. Naval blockade, on the other hand, involves the use of naval vessels to prevent an adversary from accessing a particular area or region. Cyber warfare capabilities, such as hacking or electronic warfare, can be used to disrupt an adversary's command and control systems, preventing them from coordinating their military operations.
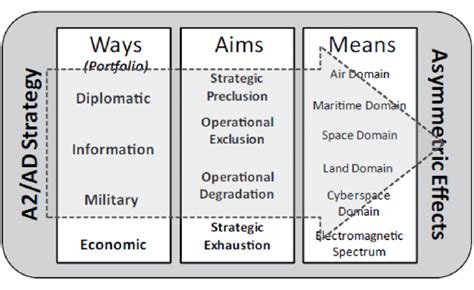
Types of A2AD Strategies
There are several types of A2AD strategies that can be employed, depending on the specific threat and the nation's military capabilities. These can include:- Active A2AD strategies: These involve the use of military force to actively deny an adversary access to a specific area or region. Examples of active A2AD strategies include missile defense systems and air defense systems.
- Passive A2AD strategies: These involve the use of non-military means to deny an adversary access to a specific area or region. Examples of passive A2AD strategies include diplomatic efforts and economic sanctions.
- Hybrid A2AD strategies: These involve the use of a combination of military and non-military means to deny an adversary access to a specific area or region. Examples of hybrid A2AD strategies include the use of cyber warfare capabilities in conjunction with missile defense systems.
Implementing A2AD Strategies
Implementing A2AD strategies requires careful planning and coordination. This can involve the use of various military branches, such as the army, navy, and air force, as well as non-military agencies, such as the diplomatic corps and intelligence agencies. The first step in implementing A2AD strategies is to identify the specific threat and the area or region that needs to be protected. This can involve conducting a thorough risk assessment, using intelligence gathering and analysis to determine the likelihood and potential impact of an attack.
Once the threat and area or region have been identified, the next step is to develop a comprehensive A2AD strategy. This can involve the use of various military capabilities, such as missile defense systems and air defense systems, as well as non-military means, such as diplomatic efforts and economic sanctions. The A2AD strategy should be tailored to the specific threat and area or region, taking into account the nation's military capabilities and the potential risks and benefits of different courses of action.
Challenges and Limitations
While A2AD strategies can be highly effective in denying an adversary access to a specific area or region, there are also several challenges and limitations that need to be considered. One of the main challenges is the potential for an adversary to use asymmetric tactics, such as guerrilla warfare or cyber attacks, to bypass or disrupt A2AD systems. Another challenge is the potential for A2AD strategies to escalate tensions or provoke an adversary into launching a military attack.Real-World Examples of A2AD Strategies
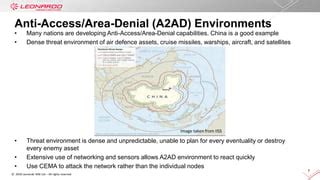
There are several real-world examples of A2AD strategies in action. One example is the use of missile defense systems by the United States and its allies to protect against ballistic missile attacks. Another example is the use of air defense systems by nations such as Russia and China to protect their airspace from incoming aircraft. Naval blockade has also been used by nations such as the United States and the United Kingdom to prevent adversaries from accessing specific areas or regions.
Future of A2AD Strategies
The future of A2AD strategies is likely to be shaped by advances in technology and changes in the global security environment. One of the main trends is the increasing use of cyber warfare capabilities to disrupt or disable A2AD systems. Another trend is the development of new military technologies, such as hypersonic missiles and advanced air defense systems, which can be used to enhance A2AD capabilities.Gallery of A2AD Strategies
A2AD Strategies Image Gallery








Frequently Asked Questions
What is Anti-Access Area Denial (A2AD)?
+Anti-Access Area Denial (A2AD) refers to the use of military capabilities to prevent or restrict an adversary's ability to access or operate within a specific area or region.
What are the benefits of A2AD strategies?
+The benefits of A2AD strategies include providing a nation with a significant military advantage, reducing the risk of military escalation, and protecting a nation's economic interests.
What are the challenges and limitations of A2AD strategies?
+The challenges and limitations of A2AD strategies include the potential for an adversary to use asymmetric tactics, the potential for A2AD strategies to escalate tensions, and the need for careful planning and coordination.
What is the future of A2AD strategies?
+The future of A2AD strategies is likely to be shaped by advances in technology and changes in the global security environment, including the increasing use of cyber warfare capabilities and the development of new military technologies.
How can A2AD strategies be implemented?
+A2AD strategies can be implemented through the use of various military capabilities, such as missile defense systems and air defense systems, as well as non-military means, such as diplomatic efforts and economic sanctions.
In conclusion, A2AD strategies are a crucial component of modern warfare, providing nations with a significant military advantage and protecting their vital interests. By understanding the benefits, challenges, and limitations of A2AD strategies, nations can develop effective A2AD capabilities that enhance their national security. We invite you to share your thoughts on A2AD strategies and their role in modern warfare. Please comment below and share this article with others who may be interested in this topic.
