Intro
Discover how vectored attacks manipulate victims through social engineering, phishing, and malware, exploiting vulnerabilities with precision tactics and cyber threats.
The world of cybersecurity is constantly evolving, with new threats and vulnerabilities emerging every day. One of the most significant risks to individuals and organizations is the vector attack, which can compromise even the most secure systems. Vector attacks are a type of cyber threat that uses multiple entry points to gain access to a network or system. In this article, we will explore five ways you got vectored and provide tips on how to protect yourself from these types of attacks.
Vector attacks are a significant concern for individuals and organizations because they can be difficult to detect and prevent. These attacks often use social engineering tactics, such as phishing and spear phishing, to trick users into revealing sensitive information or clicking on malicious links. Once a vector attack is successful, the attacker can gain access to sensitive data, disrupt operations, and cause significant financial losses. It is essential to understand the different types of vector attacks and how to prevent them to protect yourself and your organization from these threats.
The importance of cybersecurity cannot be overstated, and it is crucial to stay informed about the latest threats and vulnerabilities. By understanding the different types of vector attacks and how to prevent them, individuals and organizations can take steps to protect themselves and their sensitive data. In this article, we will provide an in-depth look at five ways you got vectored and offer practical tips on how to prevent these types of attacks.
Introduction to Vector Attacks
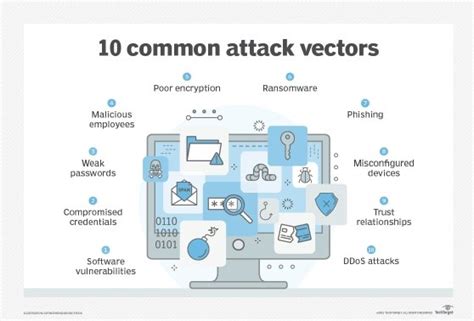
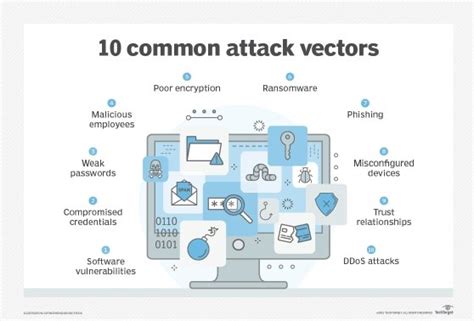
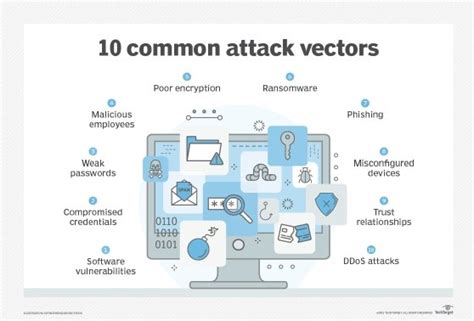
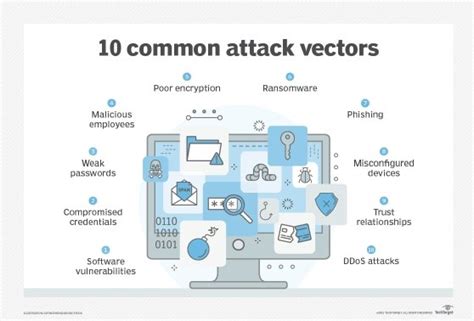
Types of Vector Attacks
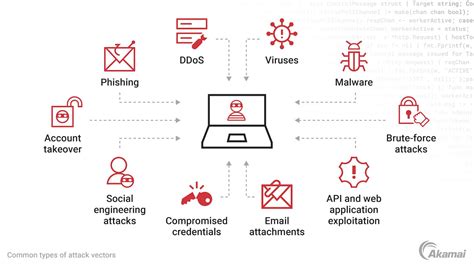
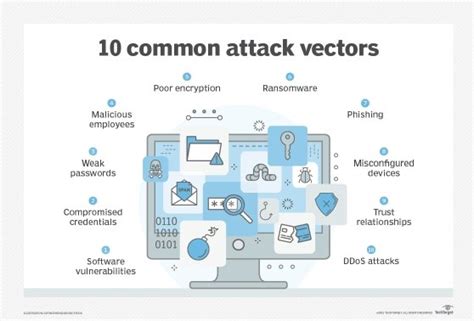
There are several types of vector attacks, including: * Phishing attacks: These attacks use fake emails or websites to trick users into revealing sensitive information, such as passwords or credit card numbers. * Spear phishing attacks: These attacks use targeted emails or messages to trick specific individuals into revealing sensitive information. * Watering hole attacks: These attacks use compromised websites or networks to infect users' devices with malware. * Drive-by downloads: These attacks use malicious code to infect users' devices when they visit a compromised website.5 Ways You Got Vectored
How to Prevent Vector Attacks
To prevent vector attacks, it is essential to take a proactive approach to cybersecurity. Here are some tips to help you protect yourself: * Use antivirus software and keep it up to date. * Avoid clicking on suspicious links or attachments. * Use strong passwords and keep them confidential. * Use a virtual private network (VPN) when connecting to public networks. * Keep your operating system and software up to date.Best Practices for Cybersecurity

Cybersecurity Tools and Resources
There are many cybersecurity tools and resources available to help you protect yourself from vector attacks and other cyber threats. Here are some options to consider: * Antivirus software: Antivirus software can help detect and remove malware from your device. * Firewall: A firewall can help block unauthorized access to your network. * VPN: A VPN can help encrypt your internet traffic and protect your data when using public networks. * Password manager: A password manager can help generate and store unique passwords.Gallery of Vector Attack Images
Vector Attack Image Gallery



Frequently Asked Questions
What is a vector attack?
+A vector attack is a type of cyber threat that uses multiple entry points to gain access to a network or system.
How can I prevent vector attacks?
+To prevent vector attacks, use antivirus software, avoid clicking on suspicious links or attachments, use strong passwords, and keep your operating system and software up to date.
What are the consequences of a vector attack?
+The consequences of a vector attack can include sensitive data theft, disruption of operations, and significant financial losses.
How can I stay safe online?
+To stay safe online, use two-factor authentication, use a password manager, avoid using public computers or public networks for sensitive activities, and regularly back up your data.
What are some common types of vector attacks?
+Some common types of vector attacks include phishing attacks, spear phishing attacks, watering hole attacks, and drive-by downloads.
In
Final Thoughts

We hope this article has provided you with valuable information about vector attacks and how to prevent them. If you have any questions or comments, please feel free to share them below. Additionally, if you found this article helpful, please consider sharing it with your friends and family to help spread awareness about cybersecurity. Together, we can create a safer online community and protect ourselves from the threats of vector attacks.
