Intro
Boost cybersecurity with 5 cyber ops tips, including threat intel, incident response, and vulnerability management, to enhance security operations and prevent cyber threats.
The world of cyber operations is a complex and ever-evolving field that requires a deep understanding of technology, strategy, and human behavior. As the reliance on digital systems continues to grow, the importance of effective cyber ops cannot be overstated. In this article, we will delve into the key aspects of cyber operations, exploring the benefits, challenges, and best practices for success. Whether you are a seasoned professional or just starting to explore the world of cyber ops, this article is designed to provide valuable insights and practical advice.
The field of cyber operations is vast and multifaceted, encompassing everything from network security and threat analysis to incident response and digital forensics. As technology advances and new threats emerge, the need for skilled cyber operators has never been greater. By understanding the principles and techniques of cyber ops, individuals and organizations can better protect themselves against cyber threats and stay ahead of the curve in the ever-changing digital landscape.
Effective cyber operations require a combination of technical expertise, strategic thinking, and collaboration. It involves not only understanding the technical aspects of digital systems but also being able to analyze and respond to threats in a timely and effective manner. Cyber ops is a team effort, requiring communication and coordination between different stakeholders to ensure the security and integrity of digital assets. By adopting a proactive and adaptive approach to cyber ops, organizations can reduce the risk of cyber attacks and minimize the impact of breaches when they do occur.
Cyber Ops Fundamentals
To succeed in the field of cyber operations, it is essential to have a solid understanding of the fundamentals. This includes knowledge of network protocols, operating systems, and software applications, as well as an understanding of threat analysis, risk management, and incident response. Cyber ops professionals must also stay up-to-date with the latest technologies and threats, continually updating their skills and knowledge to stay ahead of the curve.
Key Components of Cyber Ops
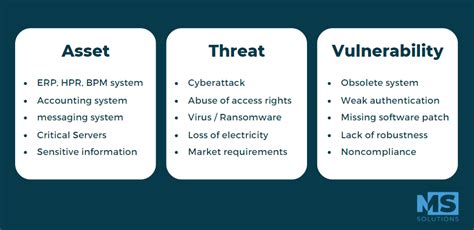
Some of the key components of cyber operations include: * Network security: This involves protecting digital networks from unauthorized access, use, disclosure, disruption, modification, or destruction. * Threat analysis: This involves identifying and analyzing potential threats to digital assets, including malware, phishing attacks, and other types of cyber threats. * Incident response: This involves responding to and managing cyber security incidents, including containment, eradication, recovery, and post-incident activities. * Digital forensics: This involves collecting, analyzing, and preserving digital evidence to investigate cyber crimes and other security incidents.Cyber Ops Tips and Best Practices
Here are five cyber ops tips and best practices to help individuals and organizations improve their cyber security posture:
- Implement a defense-in-depth strategy: This involves using multiple layers of security controls to protect digital assets, including firewalls, intrusion detection systems, and encryption.
- Conduct regular security audits and risk assessments: This involves identifying and assessing potential security risks and vulnerabilities, and implementing measures to mitigate or remediate them.
- Use strong passwords and authentication: This involves using complex passwords and multi-factor authentication to prevent unauthorized access to digital assets.
- Keep software and systems up-to-date: This involves regularly updating and patching software and systems to prevent exploitation of known vulnerabilities.
- Provide ongoing training and awareness: This involves providing regular training and awareness programs to educate users about cyber security best practices and the latest threats.
Cyber Ops Tools and Technologies
Some of the key tools and technologies used in cyber operations include: * Security information and event management (SIEM) systems * Intrusion detection and prevention systems (IDPS) * Firewalls and virtual private networks (VPNs) * Encryption and decryption tools * Digital forensics and incident response toolsCyber Ops Challenges and Limitations

Despite the importance of cyber operations, there are several challenges and limitations that individuals and organizations may face. These include:
- Limited resources: Cyber ops requires significant resources, including personnel, equipment, and budget.
- Evolving threats: Cyber threats are constantly evolving, making it challenging to stay ahead of the curve.
- Complexity: Cyber ops involves complex technologies and systems, which can be difficult to understand and manage.
- Regulatory requirements: Cyber ops must comply with various regulatory requirements, including data protection and privacy laws.
Cyber Ops Career Paths and Opportunities
Some of the key career paths and opportunities in cyber operations include: * **Cyber security analyst**: This involves analyzing and responding to cyber security incidents, as well as implementing security measures to prevent future incidents. * **Incident response specialist**: This involves responding to and managing cyber security incidents, including containment, eradication, recovery, and post-incident activities. * **Digital forensics expert**: This involves collecting, analyzing, and preserving digital evidence to investigate cyber crimes and other security incidents. * **Chief information security officer (CISO)**: This involves overseeing and managing an organization's overall cyber security strategy and posture.Cyber Ops Training and Education

To succeed in the field of cyber operations, it is essential to have the right training and education. This includes:
- Formal education: A degree in computer science, cyber security, or a related field can provide a solid foundation for a career in cyber ops.
- Certifications: Certifications such as CompTIA Security+ and CISSP can demonstrate expertise and knowledge in cyber security.
- Online courses and training programs: Online courses and training programs can provide ongoing education and training in cyber ops, including the latest threats and technologies.
Cyber Ops Community and Resources
Some of the key resources and communities for cyber operations include: * **Cyber security blogs and websites**: Websites such as Cybersecurity Ventures and The Hacker News provide news, information, and resources on cyber security. * **Cyber security conferences and events**: Conferences such as Black Hat and DEF CON provide opportunities for networking and learning about the latest cyber security threats and technologies. * **Cyber security forums and discussion groups**: Online forums and discussion groups such as Reddit's netsec community provide opportunities for networking and discussing cyber security topics.Gallery of Cyber Ops Images
Cyber Ops Image Gallery









Frequently Asked Questions
What is cyber operations?
+Cyber operations is the use of cyber capabilities to achieve strategic objectives in or through cyberspace.
What are the benefits of cyber operations?
+The benefits of cyber operations include improved security, increased efficiency, and enhanced competitiveness.
What are the challenges of cyber operations?
+The challenges of cyber operations include limited resources, evolving threats, and complexity.
How can I get started in cyber operations?
+To get started in cyber operations, you can pursue formal education, obtain certifications, and participate in online courses and training programs.
What are the career paths in cyber operations?
+The career paths in cyber operations include cyber security analyst, incident response specialist, digital forensics expert, and chief information security officer (CISO).
In conclusion, cyber operations is a critical component of modern security and defense strategies. By understanding the principles and techniques of cyber ops, individuals and organizations can better protect themselves against cyber threats and stay ahead of the curve in the ever-changing digital landscape. Whether you are a seasoned professional or just starting to explore the world of cyber ops, we hope this article has provided valuable insights and practical advice to help you succeed in this exciting and rapidly evolving field. We encourage you to share your thoughts and experiences in the comments below, and to continue the conversation on social media using the hashtag #cyberops. Together, we can work towards a safer and more secure digital future.
