Intro
Discover 5 ways Click Military works, leveraging tactical clicker games, strategic military tactics, and immersive gameplay, enhancing clicker strategy and military click games experience.
The concept of click military, also known as clickjacking or click manipulation, has been a topic of interest in recent years. It refers to the use of deceptive tactics to manipulate users into clicking on something they did not intend to click on. This can be done for various purposes, including generating revenue, stealing sensitive information, or spreading malware. In this article, we will explore the different ways click military works and how it can be used to achieve various goals.
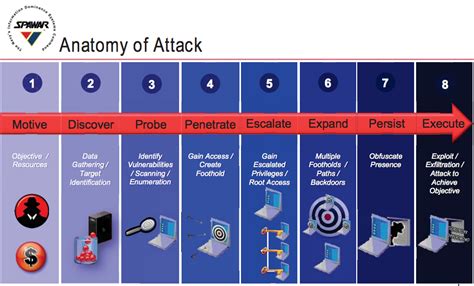
Click military is a type of cyber attack that involves tricking users into clicking on a link or button that appears to be legitimate but actually leads to a malicious website or downloads malware onto their device. This can be done through various means, including social engineering, phishing, and exploitation of vulnerabilities in software or hardware. The goal of click military is to manipulate users into performing an action that they did not intend to perform, often with the aim of generating revenue or stealing sensitive information.
One of the most common ways click military works is through the use of social engineering tactics. Social engineering involves manipulating individuals into performing a specific action or divulging sensitive information. This can be done through various means, including phishing emails, fake websites, or fake social media profiles. For example, a phishing email may be sent to a user that appears to be from a legitimate company, such as a bank or online retailer. The email may ask the user to click on a link to update their account information or to verify their identity. However, the link actually leads to a malicious website that steals the user's login credentials or installs malware onto their device.
Another way click military works is through the exploitation of vulnerabilities in software or hardware. This can involve the use of exploit kits, which are software tools that exploit known vulnerabilities in software or hardware to gain unauthorized access to a device or network. For example, an exploit kit may be used to exploit a vulnerability in a web browser or operating system, allowing an attacker to gain control of a user's device or steal sensitive information.
Understanding Click Military Tactics
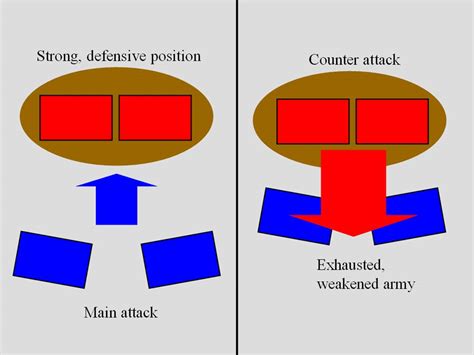
Click military tactics can be used to achieve various goals, including generating revenue, stealing sensitive information, or spreading malware. One of the most common goals of click military is to generate revenue through the use of pay-per-click advertising. Pay-per-click advertising involves paying a fee each time a user clicks on an ad. Click military can be used to manipulate users into clicking on ads, generating revenue for the attacker.
Types of Click Military Attacks
Click military attacks can take various forms, including:- Clickjacking: This involves tricking users into clicking on a link or button that appears to be legitimate but actually leads to a malicious website or downloads malware onto their device.
- Phishing: This involves sending fake emails or messages that appear to be from a legitimate company, such as a bank or online retailer, in an attempt to steal sensitive information.
- Exploit kits: These are software tools that exploit known vulnerabilities in software or hardware to gain unauthorized access to a device or network.
How Click Military Works
Click military works by manipulating users into performing an action that they did not intend to perform. This can be done through various means, including social engineering, phishing, and exploitation of vulnerabilities in software or hardware. The goal of click military is to generate revenue, steal sensitive information, or spread malware.
Click Military Techniques
Click military techniques can include:- Social engineering: This involves manipulating individuals into performing a specific action or divulging sensitive information.
- Phishing: This involves sending fake emails or messages that appear to be from a legitimate company, such as a bank or online retailer, in an attempt to steal sensitive information.
- Exploit kits: These are software tools that exploit known vulnerabilities in software or hardware to gain unauthorized access to a device or network.
Consequences of Click Military

The consequences of click military can be severe, including financial loss, identity theft, and compromised device or network security. Click military can also be used to spread malware, which can lead to further consequences, such as data loss or device compromise.
Protecting Against Click Military
To protect against click military, it is essential to be aware of the tactics and techniques used by attackers. This can include being cautious when clicking on links or buttons, avoiding suspicious emails or messages, and keeping software and hardware up to date with the latest security patches.Best Practices for Avoiding Click Military
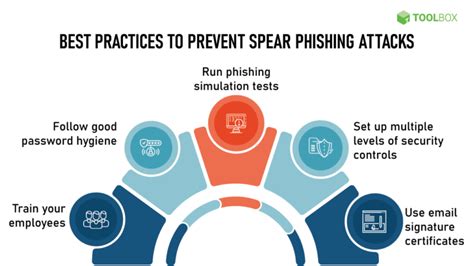
Best practices for avoiding click military include:
- Being cautious when clicking on links or buttons
- Avoiding suspicious emails or messages
- Keeping software and hardware up to date with the latest security patches
- Using antivirus software and a firewall to protect against malware and unauthorized access
- Being aware of the tactics and techniques used by attackers
Click Military Prevention Tips
Click military prevention tips can include:- Using strong passwords and keeping them confidential
- Avoiding using public computers or public Wi-Fi to access sensitive information
- Keeping browser and operating system up to date with the latest security patches
- Using a virtual private network (VPN) to encrypt internet traffic
- Being cautious when clicking on links or buttons, especially in emails or messages from unknown senders
Click Military and Cybersecurity

Click military is a significant threat to cybersecurity, as it can be used to manipulate users into performing actions that compromise device or network security. To protect against click military, it is essential to have a comprehensive cybersecurity strategy in place, including antivirus software, a firewall, and regular security updates.
Cybersecurity Measures
Cybersecurity measures can include:- Using antivirus software and a firewall to protect against malware and unauthorized access
- Keeping software and hardware up to date with the latest security patches
- Using strong passwords and keeping them confidential
- Avoiding using public computers or public Wi-Fi to access sensitive information
- Being cautious when clicking on links or buttons, especially in emails or messages from unknown senders
Gallery of Click Military Images
Click Military Image Gallery









What is click military?
+Click military, also known as clickjacking or click manipulation, refers to the use of deceptive tactics to manipulate users into clicking on something they did not intend to click on.
How does click military work?
+Click military works by manipulating users into performing an action that they did not intend to perform, often through social engineering, phishing, or exploitation of vulnerabilities in software or hardware.
What are the consequences of click military?
+The consequences of click military can be severe, including financial loss, identity theft, and compromised device or network security.
How can I protect against click military?
+To protect against click military, it is essential to be aware of the tactics and techniques used by attackers, keep software and hardware up to date with the latest security patches, and use antivirus software and a firewall to protect against malware and unauthorized access.
What are the best practices for avoiding click military?
+Best practices for avoiding click military include being cautious when clicking on links or buttons, avoiding suspicious emails or messages, keeping software and hardware up to date with the latest security patches, and using antivirus software and a firewall to protect against malware and unauthorized access.
In conclusion, click military is a significant threat to cybersecurity, and it is essential to be aware of the tactics and techniques used by attackers to protect against it. By understanding how click military works and taking steps to prevent it, individuals and organizations can reduce the risk of financial loss, identity theft, and compromised device or network security. We encourage readers to share their experiences and tips for avoiding click military in the comments section below. Additionally, we invite readers to explore our other articles on cybersecurity and online safety to stay informed and protected in the digital age.
