Intro
Discover Cybersecurity Explained, covering threat protection, data security, and network safety to prevent cyber attacks and ensure online protection with latest security measures.
The world of technology has brought about numerous benefits and advancements, but it has also introduced a new wave of threats and risks. Cybersecurity is a critical aspect of the digital age, and its importance cannot be overstated. As technology continues to evolve, the need for robust cybersecurity measures has become more pressing than ever. In this article, we will delve into the world of cybersecurity, exploring its significance, key concepts, and best practices for individuals and organizations.
The rapid growth of the internet and connected devices has created a vast attack surface, making it easier for cybercriminals to launch attacks and exploit vulnerabilities. Cyber threats can take many forms, including malware, phishing, ransomware, and denial-of-service (DoS) attacks. These threats can have devastating consequences, ranging from financial loss and data breaches to compromised national security and disrupted critical infrastructure. As such, it is essential to understand the fundamentals of cybersecurity and take proactive steps to protect against these threats.
Cybersecurity is a multifaceted field that encompasses a range of disciplines, including computer science, engineering, and social sciences. It involves the use of various technologies, processes, and practices to prevent, detect, and respond to cyber threats. Effective cybersecurity requires a comprehensive approach that addresses the entire lifecycle of a threat, from prevention and detection to response and recovery. By adopting a proactive and layered approach to cybersecurity, individuals and organizations can significantly reduce the risk of cyber attacks and minimize the impact of a breach.
Introduction to Cybersecurity

Cybersecurity is a critical component of the digital ecosystem, and its importance extends beyond the realm of technology. It is a business imperative, a social responsibility, and a national security concern. As such, it is essential to understand the key concepts and principles of cybersecurity, including threat intelligence, risk management, and incident response. By grasping these fundamentals, individuals and organizations can develop effective cybersecurity strategies that align with their goals and objectives.
Key Concepts in Cybersecurity
Some of the key concepts in cybersecurity include: * Threat intelligence: The process of gathering and analyzing information about potential threats to identify vulnerabilities and anticipate attacks. * Risk management: The process of identifying, assessing, and mitigating risks to minimize the impact of a cyber attack. * Incident response: The process of responding to and managing a cyber attack, including containment, eradication, recovery, and post-incident activities. * Network security: The practice of protecting computer networks from unauthorized access, use, disclosure, disruption, modification, or destruction. * Cryptography: The practice of secure communication by transforming plaintext into unreadable ciphertext to protect data from unauthorized access.Cyber Threats and Vulnerabilities

Cyber threats can take many forms, including malware, phishing, ransomware, and denial-of-service (DoS) attacks. These threats can exploit vulnerabilities in software, hardware, and human behavior to gain unauthorized access to systems, data, and networks. Some of the most common cyber threats include:
- Malware: Software designed to harm or exploit a computer system, including viruses, worms, and trojans.
- Phishing: A type of social engineering attack that uses email, phone, or text messages to trick individuals into revealing sensitive information.
- Ransomware: A type of malware that encrypts data and demands payment in exchange for the decryption key.
- Denial-of-service (DoS) attacks: A type of attack that overwhelms a system or network with traffic to make it unavailable to users.
Types of Cyber Attacks
Some of the most common types of cyber attacks include: * Network attacks: Attacks that target computer networks, including DoS attacks, man-in-the-middle (MitM) attacks, and network scanning. * System attacks: Attacks that target computer systems, including buffer overflow attacks, SQL injection attacks, and cross-site scripting (XSS) attacks. * Data attacks: Attacks that target data, including data breaches, data theft, and data manipulation. * Social engineering attacks: Attacks that target human behavior, including phishing, pretexting, and baiting.Cybersecurity Measures and Best Practices

Effective cybersecurity requires a comprehensive approach that addresses the entire lifecycle of a threat. Some of the key cybersecurity measures and best practices include:
- Implementing firewalls and intrusion detection systems to prevent unauthorized access.
- Using antivirus software and malware detection tools to identify and remove malware.
- Encrypting data to protect it from unauthorized access.
- Implementing secure authentication and authorization mechanisms to control access to systems and data.
- Conducting regular security audits and vulnerability assessments to identify and mitigate risks.
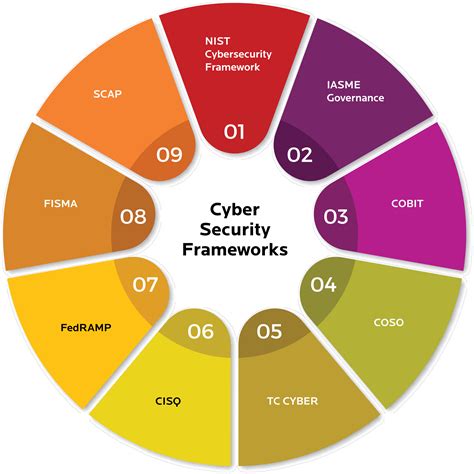
Cybersecurity Frameworks and Standards
Some of the most common cybersecurity frameworks and standards include: * NIST Cybersecurity Framework: A framework that provides a structured approach to managing and reducing cybersecurity risk. * ISO 27001: A standard that provides a framework for implementing and maintaining an information security management system (ISMS). * PCI-DSS: A standard that provides a framework for securing payment card data. * HIPAA: A standard that provides a framework for securing protected health information (PHI).Cybersecurity for Individuals

Individuals can take several steps to protect themselves from cyber threats, including:
- Using strong passwords and enabling two-factor authentication.
- Keeping software and operating systems up to date.
- Being cautious when clicking on links or opening attachments from unknown sources.
- Using antivirus software and malware detection tools.
- Implementing a firewall and intrusion detection system.
Online Safety Tips
Some of the most important online safety tips include: * Being aware of phishing scams and suspicious emails. * Using secure connections when browsing the internet. * Avoiding public Wi-Fi when accessing sensitive information. * Using a virtual private network (VPN) when accessing public Wi-Fi. * Keeping personal data and financial information secure.Cybersecurity for Organizations

Organizations can take several steps to protect themselves from cyber threats, including:
- Implementing a comprehensive cybersecurity strategy.
- Conducting regular security audits and vulnerability assessments.
- Implementing secure authentication and authorization mechanisms.
- Using encryption to protect data.
- Providing cybersecurity training and awareness programs for employees.
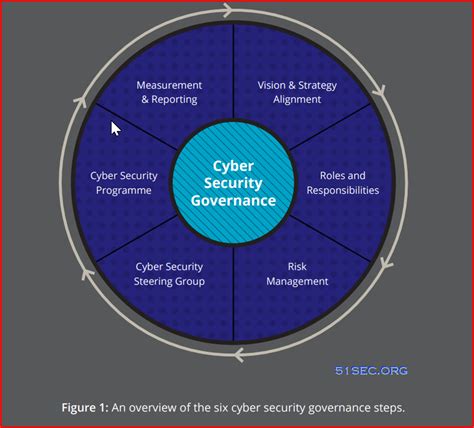
Cybersecurity Governance and Risk Management
Some of the most important cybersecurity governance and risk management practices include: * Establishing a cybersecurity governance framework. * Conducting regular risk assessments and mitigation activities. * Implementing incident response and disaster recovery plans. * Providing cybersecurity awareness and training programs for employees. * Continuously monitoring and evaluating cybersecurity controls and processes.Cybersecurity Image Gallery








What is cybersecurity?
+Cybersecurity is the practice of protecting computer systems, networks, and data from unauthorized access, use, disclosure, disruption, modification, or destruction.
Why is cybersecurity important?
+Cybersecurity is important because it helps protect against cyber threats, which can have devastating consequences, including financial loss, data breaches, and compromised national security.
What are some common cyber threats?
+Some common cyber threats include malware, phishing, ransomware, and denial-of-service (DoS) attacks.
How can individuals protect themselves from cyber threats?
+Individuals can protect themselves from cyber threats by using strong passwords, keeping software and operating systems up to date, being cautious when clicking on links or opening attachments from unknown sources, and using antivirus software and malware detection tools.
What are some best practices for cybersecurity?
+Some best practices for cybersecurity include implementing a comprehensive cybersecurity strategy, conducting regular security audits and vulnerability assessments, implementing secure authentication and authorization mechanisms, using encryption to protect data, and providing cybersecurity training and awareness programs for employees.
In conclusion, cybersecurity is a critical aspect of the digital age, and its importance cannot be overstated. By understanding the key concepts and principles of cybersecurity, individuals and organizations can develop effective strategies to protect against cyber threats and minimize the impact of a breach. We encourage readers to share their thoughts and experiences on cybersecurity in the comments section below. Additionally, we invite readers to share this article with others who may benefit from this information. By working together, we can create a safer and more secure digital environment for everyone.
