Intro
Enhance cybersecurity with 5 US Army cyber tips, featuring threat protection, network security, and cyber awareness to prevent hacking and data breaches, ensuring online safety and digital defense.
Cybersecurity is a critical aspect of modern life, and the US Army has been at the forefront of developing strategies to protect against cyber threats. The US Army's cyber tips are designed to help individuals and organizations protect themselves from cyber attacks and maintain the security of their digital information. In this article, we will explore five US Army cyber tips that can help you enhance your cybersecurity posture.
The importance of cybersecurity cannot be overstated. With the increasing reliance on digital technologies, the risk of cyber attacks has grown exponentially. Cyber attacks can result in significant financial losses, damage to reputation, and even compromise national security. Therefore, it is essential to take proactive measures to protect against cyber threats. The US Army's cyber tips provide valuable guidance on how to do so.
The US Army's cyber tips are based on the latest research and best practices in cybersecurity. They are designed to be easy to understand and implement, making them accessible to individuals and organizations of all sizes. By following these tips, you can significantly reduce the risk of cyber attacks and protect your digital information. In the following sections, we will delve into each of the five US Army cyber tips and explore how you can apply them to enhance your cybersecurity posture.
Tip 1: Use Strong Passwords

Best Practices for Password Management
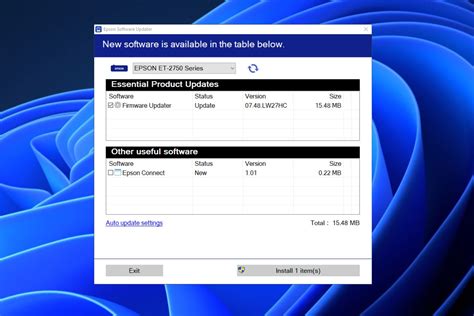
To use strong passwords effectively, follow these best practices: * Use a password manager to generate and store unique, complex passwords for each of your accounts. * Avoid using the same password for multiple accounts. * Change your passwords regularly, ideally every 60-90 days. * Use two-factor authentication (2FA) whenever possible to add an extra layer of security.Tip 2: Keep Your Software Up-to-Date
Benefits of Regular Software Updates
Regular software updates offer several benefits, including: * Improved security: Software updates often include patches for security vulnerabilities, which can help protect against cyber attacks. * Enhanced performance: Software updates can improve the performance and stability of your software, reducing the risk of crashes and errors. * New features: Software updates often include new features and functionality, which can enhance your overall user experience.Tip 3: Be Cautious of Phishing Attacks
How to Identify Phishing Attacks
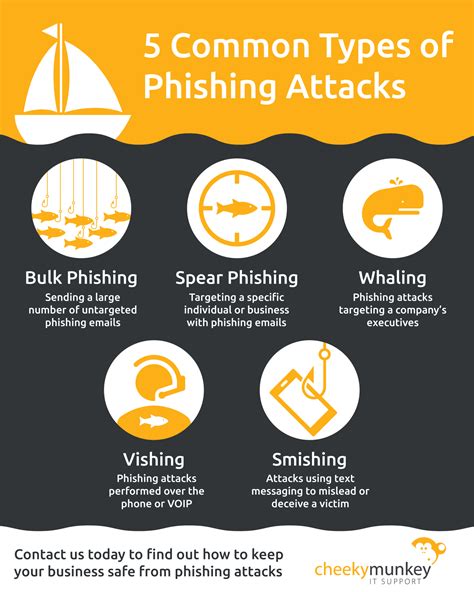
To identify phishing attacks, look out for the following signs: * Urgency: Phishing attacks often create a sense of urgency, attempting to trick you into acting quickly without thinking. * Spelling and grammar mistakes: Phishing attacks often include spelling and grammar mistakes, which can be a sign of a scam. * Suspicious links: Be cautious of links that are suspicious or unfamiliar, and never click on them without verifying their authenticity.Tip 4: Use Encryption
Types of Encryption
There are several types of encryption, including: * Symmetric encryption: Symmetric encryption uses the same key for encryption and decryption. * Asymmetric encryption: Asymmetric encryption uses a pair of keys, one for encryption and another for decryption. * Hashing: Hashing is a type of encryption that creates a fixed-size string of characters from input data.Tip 5: Monitor Your Accounts

Benefits of Account Monitoring
Account monitoring offers several benefits, including: * Early detection of cyber attacks: Monitoring your accounts can help you detect cyber attacks early, reducing the risk of financial losses. * Prevention of financial losses: By detecting suspicious activity early, you can prevent financial losses and protect your assets. * Improved security: Account monitoring can help you identify vulnerabilities in your accounts, allowing you to take proactive measures to improve security.Cybersecurity Image Gallery










What is the most effective way to protect against cyber attacks?
+The most effective way to protect against cyber attacks is to use a combination of security measures, including strong passwords, software updates, and encryption.
How can I identify phishing attacks?
+To identify phishing attacks, look out for signs such as urgency, spelling and grammar mistakes, and suspicious links. Verify the authenticity of the message before responding, and never click on suspicious links or provide sensitive information via email or messaging apps.
What is the importance of account monitoring?
+Account monitoring is essential for detecting cyber attacks and preventing financial losses. Regularly review your bank and credit card statements to detect any suspicious activity, and set up alerts for large or unusual transactions.
How can I improve my cybersecurity posture?
+To improve your cybersecurity posture, follow the US Army's cyber tips, including using strong passwords, keeping your software up-to-date, being cautious of phishing attacks, using encryption, and monitoring your accounts. Additionally, stay informed about the latest cybersecurity threats and best practices, and take proactive measures to protect your digital information.
What is the role of encryption in cybersecurity?
+Encryption plays a critical role in cybersecurity by protecting sensitive information from unauthorized access. Encryption scrambles data, making it unreadable to anyone without the decryption key. Use encryption to protect sensitive information such as financial data, personal identifiable information, and confidential business information.
In conclusion, the US Army's cyber tips provide valuable guidance on how to protect against cyber attacks and maintain the security of your digital information. By following these tips, you can significantly reduce the risk of cyber attacks and protect your assets. Remember to stay informed about the latest cybersecurity threats and best practices, and take proactive measures to protect your digital information. Share this article with your friends and family to help them improve their cybersecurity posture, and comment below with any questions or concerns you may have. Together, we can create a safer and more secure digital environment.
