Intro
Boost cybersecurity with 5 expert tips for Taureans, featuring threat protection, cyber awareness, and online safety measures to prevent hacking and data breaches.
As technology advances, cybersecurity has become a critical aspect of our daily lives. With the increasing number of cyber threats, it's essential to take proactive measures to protect ourselves and our organizations from potential attacks. For individuals and businesses born under the sign of Taurus, cybersecurity is not just a necessity, but a vital investment in their digital well-being. In this article, we'll explore five tips for Taurean cybersecurity, focusing on practical advice and best practices to enhance your online security.
The importance of cybersecurity cannot be overstated, especially for Taureans who value stability and security. A single cyber attack can compromise sensitive information, disrupt business operations, and cause significant financial losses. Moreover, the aftermath of a cyber attack can be devastating, leading to a loss of trust and reputation. By prioritizing cybersecurity, Taureans can safeguard their digital assets, protect their reputation, and maintain the stability they cherish.
Taureans are known for their practical and reliable nature, which makes them well-suited to implement effective cybersecurity measures. By taking a proactive approach to cybersecurity, Taureans can prevent potential threats, detect suspicious activity, and respond quickly to incidents. This approach not only protects their digital assets but also provides peace of mind, allowing them to focus on their personal and professional goals. Whether you're a individual or a business owner, these five tips will help you enhance your cybersecurity posture and stay safe in the digital world.
Understanding Cyber Threats

Types of Cyber Threats
Some common types of cyber threats include: * Malware: Malicious software designed to harm or exploit computer systems * Phishing: Fraudulent attempts to obtain sensitive information * Ransomware: A type of malware that demands payment in exchange for restoring access to compromised data * Denial-of-service (DoS) attacks: Overwhelming computer systems with traffic to make them unavailable * Man-in-the-middle (MitM) attacks: Intercepting communication between two parties to steal sensitive informationImplementing Cybersecurity Measures

Cybersecurity Best Practices
Some cybersecurity best practices include: * Using antivirus software and keeping it up-to-date * Implementing firewalls and configuring them correctly * Using encryption technologies to protect sensitive information * Implementing secure password protocols, such as multi-factor authentication * Regularly backing up data and storing it securelyEnhancing Network Security

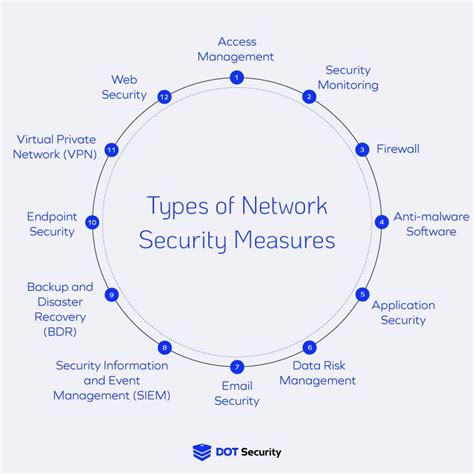
Network Security Measures
Some network security measures include: * Implementing secure protocols for wireless networks, such as WPA2 encryption and secure passwords * Using virtual private networks (VPNs) to encrypt internet traffic * Configuring firewalls to block unauthorized access to computer systems * Implementing intrusion detection and prevention systems to detect and prevent malicious activity * Regularly updating network devices and software to prevent vulnerabilitiesDeveloping a Cybersecurity Plan
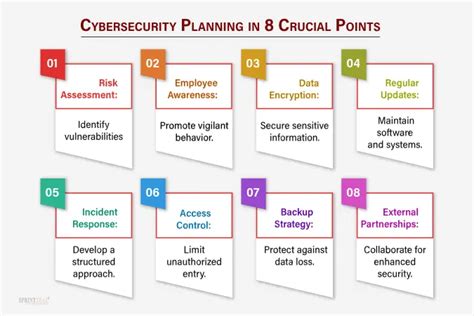
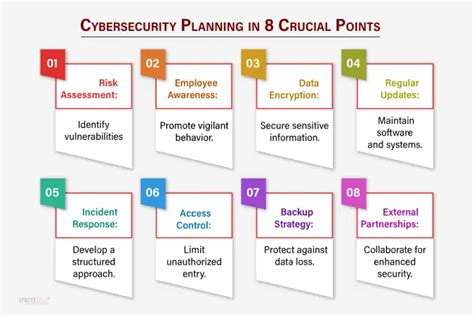
Cybersecurity Plan Components
Some components of a cybersecurity plan include: * Conducting risk assessments to identify potential vulnerabilities * Implementing incident response plans to respond to cyber attacks * Providing cybersecurity training to employees to prevent and detect cyber threats * Regularly updating software and systems to prevent vulnerabilities * Implementing secure protocols for passwords, backups, and software updatesStaying Informed about Cyber Threats

Cyber Threats Awareness
Some ways to stay informed about cyber threats include: * Following reputable sources, such as cybersecurity news outlets and government agencies * Participating in cybersecurity communities and forums to share knowledge and best practices * Attending cybersecurity conferences and workshops to learn about the latest threats and technologies * Subscribing to cybersecurity newsletters and alerts to stay up-to-date on the latest threats * Conducting regular risk assessments to identify potential vulnerabilitiesCybersecurity Image Gallery







What are the most common types of cyber threats?
+The most common types of cyber threats include malware, phishing, ransomware, and denial-of-service (DoS) attacks.
How can I protect myself from cyber threats?
+You can protect yourself from cyber threats by using antivirus software, implementing firewalls, and using encryption technologies. Additionally, you can implement secure protocols for passwords, backups, and software updates.
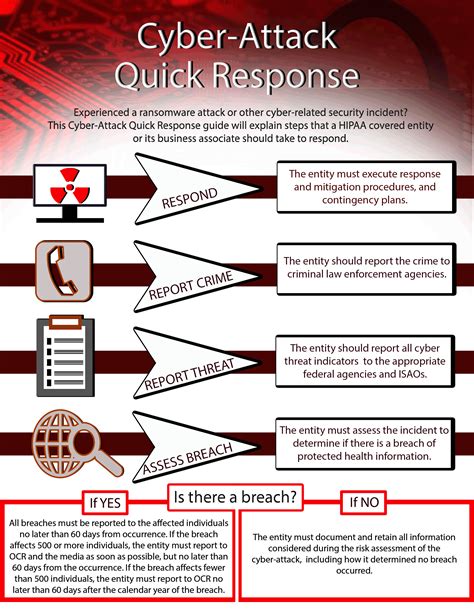
What is a cybersecurity plan, and why is it important?
+A cybersecurity plan is a comprehensive plan that outlines measures to prevent, detect, and respond to cyber threats. It is essential to have a cybersecurity plan in place to protect digital assets and respond to cyber attacks.
In conclusion, cybersecurity is a critical aspect of our daily lives, and it's essential to take proactive measures to protect ourselves and our organizations from potential cyber threats. By following these five tips, Taureans can enhance their cybersecurity posture and stay safe in the digital world. Remember to stay informed about cyber threats, implement effective cybersecurity measures, and develop a comprehensive cybersecurity plan to protect your digital assets. Share this article with your friends and family to help them stay safe online, and take the first step towards a more secure digital future.
