Intro
Unlock the 5 Tango Military Codes, exploring phonetic alphabets, radio protocols, and tactical communications, revealing secrets of military terminology, codes, and language.
The world of military codes and communication is a fascinating one, full of secrets and strategies that have been used throughout history to gain an upper hand on the battlefield. One such code that has gained significant attention in recent years is the 5 Tango code, used by military personnel to convey important information in a concise and secure manner. But what exactly is the 5 Tango code, and how does it work?
The 5 Tango code is a type of phonetic alphabet used by the military to clearly communicate letters and numbers over radio and other communication devices. This code is essential in situations where standard communication methods may be unclear or unreliable, such as in noisy environments or when communicating with people who speak different languages. By using a standardized set of codes, military personnel can ensure that their messages are conveyed accurately and efficiently, reducing the risk of misunderstandings and errors.
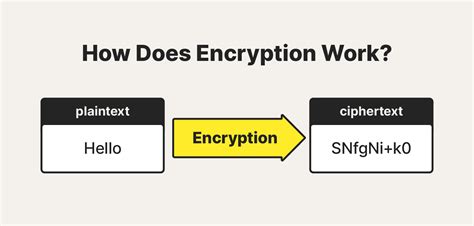
The 5 Tango code is just one example of the many military codes and communication strategies that have been developed over the years. These codes have played a crucial role in military operations, allowing personnel to convey vital information and coordinate their actions with precision and accuracy. From the basic phonetic alphabet to more complex encryption methods, military codes have been used to protect sensitive information and gain a strategic advantage on the battlefield.
As we delve deeper into the world of military codes and communication, it becomes clear that there is a rich history and complexity to this subject. From the early days of military communication to the present day, codes and ciphers have been used to convey important information and protect national security. In this article, we will explore the 5 Tango code in more detail, examining its history, uses, and significance in the context of military communication.
Introduction to Military Codes

Military codes have been used for centuries, with early examples including the Caesar cipher and other simple encryption methods. These codes were used to protect sensitive information and convey messages securely, often in situations where the enemy was likely to intercept communications. Over time, military codes have become increasingly sophisticated, incorporating advanced encryption methods and communication technologies.
The use of military codes is not limited to combat operations; they are also used in a variety of other contexts, such as intelligence gathering and diplomatic communication. In these situations, codes are used to protect sensitive information and maintain confidentiality, ensuring that only authorized personnel have access to the information.
Phonetic Alphabets and the 5 Tango Code
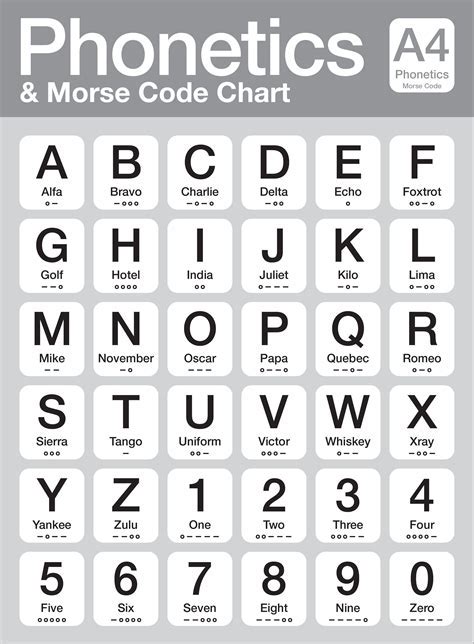
The 5 Tango code is a type of phonetic alphabet, which is a standardized set of codes used to clearly communicate letters and numbers over radio and other communication devices. This code is essential in situations where standard communication methods may be unclear or unreliable, such as in noisy environments or when communicating with people who speak different languages.
The 5 Tango code is used to convey a specific set of information, such as coordinates, call signs, or other vital data. By using a standardized set of codes, military personnel can ensure that their messages are conveyed accurately and efficiently, reducing the risk of misunderstandings and errors.
How the 5 Tango Code Works
The 5 Tango code is a simple yet effective system for conveying information. It consists of a set of codes, each corresponding to a specific letter or number. For example, the code "5 Tango" might be used to convey the number 5, while the code "Bravo" might be used to convey the letter B.By using a combination of these codes, military personnel can convey complex information in a clear and concise manner. For example, a message might be conveyed as "5 Tango, Bravo, 12, Charlie," which would correspond to the number 5, the letter B, the number 12, and the letter C.
Military Communication Strategies

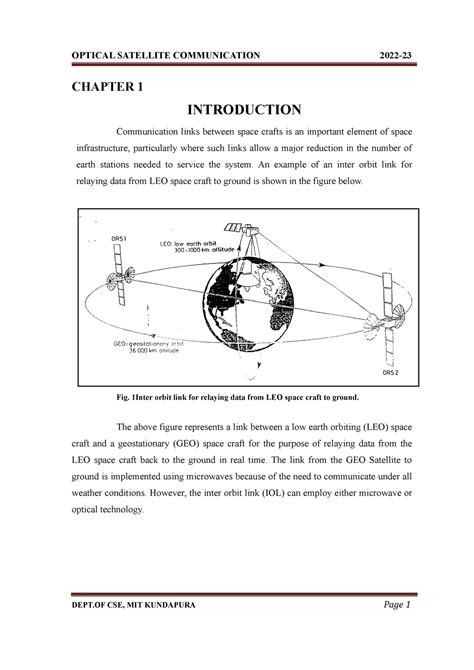
Military communication strategies are critical to the success of military operations. These strategies involve the use of a variety of techniques and technologies to convey information and coordinate actions. From basic radio communication to advanced satellite systems, military personnel use a range of methods to stay in touch and achieve their objectives.
One key aspect of military communication is the use of secure communication methods. This includes the use of encryption and other security measures to protect sensitive information from interception or eavesdropping. By using secure communication methods, military personnel can ensure that their messages are conveyed safely and efficiently, reducing the risk of compromise or interception.
Types of Military Communication
There are several types of military communication, each with its own unique characteristics and applications. These include:- Radio communication: This is one of the most common forms of military communication, involving the use of radio waves to convey information over short or long distances.
- Satellite communication: This involves the use of satellites to convey information over long distances, often in situations where other forms of communication are not available.
- Wire communication: This involves the use of wires or cables to convey information, often in situations where security is a high priority.
Each of these types of communication has its own strengths and weaknesses, and military personnel must carefully consider their options when choosing a communication method.
History of Military Codes
The history of military codes dates back centuries, with early examples including the Caesar cipher and other simple encryption methods. These codes were used to protect sensitive information and convey messages securely, often in situations where the enemy was likely to intercept communications.
Over time, military codes have become increasingly sophisticated, incorporating advanced encryption methods and communication technologies. From the early days of radio communication to the present day, codes and ciphers have been used to convey important information and protect national security.
Early Military Codes
Some of the earliest military codes include:- The Caesar cipher: This is a simple encryption method that involves shifting each letter in the alphabet by a fixed number of positions.
- The Vigenère cipher: This is a more complex encryption method that involves using a series of Caesar ciphers with different shifts.
These early codes were used to protect sensitive information and convey messages securely, often in situations where the enemy was likely to intercept communications.
Modern Military Codes
Modern military codes are highly sophisticated, incorporating advanced encryption methods and communication technologies. These codes are used to protect sensitive information and convey messages securely, often in situations where the enemy is likely to intercept communications.
Some examples of modern military codes include:
- The Advanced Encryption Standard (AES): This is a widely used encryption method that involves using a series of complex algorithms to protect data.
- The Secure Sockets Layer (SSL): This is a protocol used to secure online communications, often used in situations where sensitive information is being transmitted.
These modern codes are highly effective, providing a high level of security and protection for sensitive information.
Future of Military Codes
The future of military codes is likely to involve the use of even more advanced encryption methods and communication technologies. This may include the use of quantum computing and other emerging technologies to create highly secure and efficient codes.As military communication continues to evolve, it is likely that codes and ciphers will play an increasingly important role in protecting sensitive information and conveying messages securely.
Military Codes Image Gallery





What is the 5 Tango code?
+The 5 Tango code is a type of phonetic alphabet used by the military to clearly communicate letters and numbers over radio and other communication devices.
How does the 5 Tango code work?
+The 5 Tango code works by using a standardized set of codes to convey letters and numbers. Each code corresponds to a specific letter or number, allowing military personnel to convey complex information in a clear and concise manner.
What is the history of military codes?
+The history of military codes dates back centuries, with early examples including the Caesar cipher and other simple encryption methods. Over time, military codes have become increasingly sophisticated, incorporating advanced encryption methods and communication technologies.
What are some examples of modern military codes?
+Some examples of modern military codes include the Advanced Encryption Standard (AES) and the Secure Sockets Layer (SSL). These codes are highly effective, providing a high level of security and protection for sensitive information.
What is the future of military codes?
+The future of military codes is likely to involve the use of even more advanced encryption methods and communication technologies. This may include the use of quantum computing and other emerging technologies to create highly secure and efficient codes.
In conclusion, the 5 Tango code is a critical component of military communication, allowing personnel to convey vital information in a clear and concise manner. By understanding the history and significance of military codes, we can appreciate the importance of secure communication in protecting national security and achieving military objectives. Whether you are a military professional or simply interested in the world of codes and ciphers, this article has provided a comprehensive overview of the 5 Tango code and its role in modern military operations. We invite you to share your thoughts and questions in the comments below, and to explore further the fascinating world of military codes and communication.
