Intro
Identify covert threats with the 5 Signs Infiltrator guide, revealing suspicious behavior, security breaches, and covert operations through espionage, surveillance, and infiltration tactics.
In today's world, security and integrity are of utmost importance, whether it's in personal relationships, professional settings, or national security. The presence of an infiltrator can lead to compromised trust, leaked information, and potentially disastrous consequences. Recognizing the signs of an infiltrator is crucial for maintaining the safety and security of individuals, organizations, and communities. An infiltrator is someone who gains access to a group or organization by secretly joining it, with the intention of gathering information, causing harm, or influencing decisions from within. The methods and motivations of infiltrators can vary widely, from espionage and terrorism to corporate espionage and personal vendettas.
The importance of identifying infiltrators cannot be overstated. Their actions can lead to financial loss, reputational damage, and even physical harm. Infiltrators often use deception and manipulation to achieve their goals, making them difficult to detect. However, there are common signs and behaviors that can indicate the presence of an infiltrator. Being aware of these signs is the first step in protecting against potential threats. This knowledge empowers individuals and organizations to take proactive measures, ensuring the integrity and security of their environments.
Understanding the tactics and behaviors of infiltrators is key to recognizing and thwarting their efforts. Infiltrators often exhibit behaviors that are out of the ordinary or inconsistent with the norms of the group they have infiltrated. They might show an unusual interest in certain information or areas, be overly curious, or seem evasive when questioned about their activities or background. Identifying these behaviors requires vigilance and a keen sense of awareness. By educating oneself on the signs of infiltration, one can contribute to creating a safer and more secure community.
Introduction to Infiltrators
Infiltrators can be found in various contexts, from the digital world to physical environments. They might be individuals working alone or as part of a larger organization. The digital age has made it easier for infiltrators to operate, with cyber attacks and data breaches becoming increasingly common. In the physical world, infiltrators might join groups or organizations under false pretenses, aiming to gather intelligence or disrupt operations from within.
Signs of an Infiltrator

Recognizing the signs of an infiltrator is crucial for early detection and prevention of potential harm. Some common signs include:
- Unusual Behavior: Infiltrators may exhibit behaviors that are not typical of others within the group. This could include working irregular hours, accessing restricted areas without authorization, or showing an unusual interest in sensitive information.
- Evasiveness: When questioned about their activities or background, infiltrators might be evasive or secretive. They could provide vague answers or avoid direct questions altogether.
- Inconsistencies: Infiltrators may have inconsistencies in their story or background that, when investigated, reveal discrepancies. This could involve false credentials, unverifiable past employment, or contradictions in their personal history.
- Overly Curious: An infiltrator might ask questions that seem out of place or inappropriate, especially regarding sensitive or confidential information.
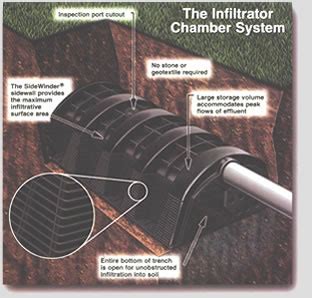
- Technical Issues: In the context of cyber security, infiltrators might introduce malware or create backdoors into a system, leading to unexplained technical issues or system vulnerabilities.
Types of Infiltrators
Infiltrators can be categorized based on their motivations and methods. Some common types include:
- Corporate Spies: These individuals infiltrate companies to steal trade secrets, intellectual property, or confidential business information.
- Cyber Hackers: Operating in the digital realm, these infiltrators use various techniques to breach security systems, steal data, or disrupt operations.
- Terrorist Infiltrators: With the goal of causing harm or promoting a political agenda, these individuals might infiltrate communities, organizations, or government agencies.
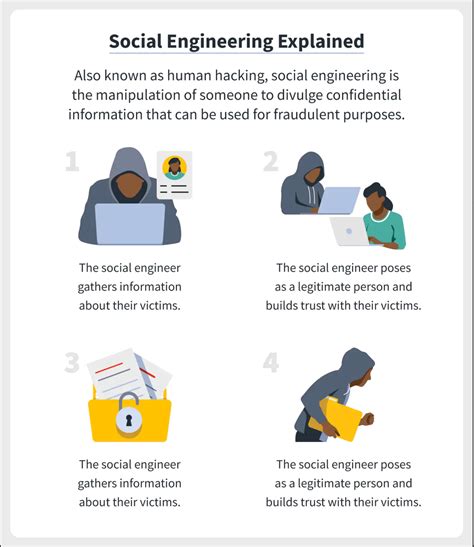
- Social Engineers: Using psychological manipulation, social engineers trick individuals into divulging confidential information or performing certain actions that compromise security.
Protecting Against Infiltrators

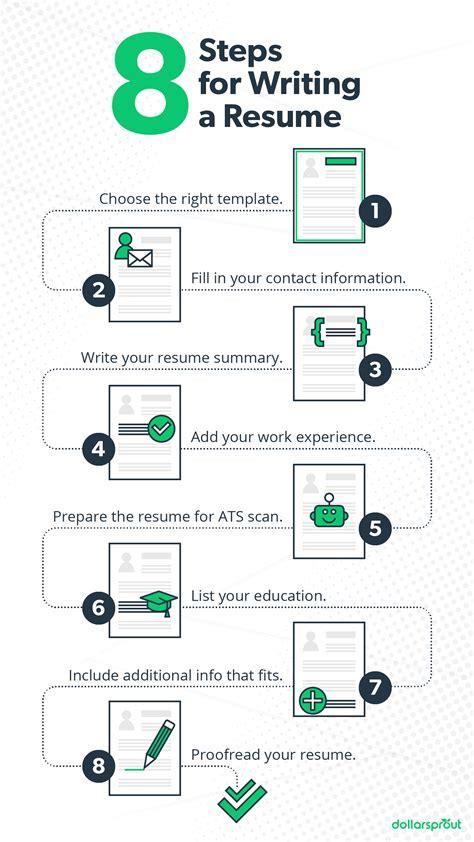
Protecting against infiltrators requires a multi-faceted approach that includes both preventive measures and proactive monitoring. Some strategies include:
- Background Checks: Conducting thorough background checks on new employees or members can help identify potential infiltrators.
- Security Awareness Training: Educating individuals about the signs of infiltration and the importance of security can prevent many types of attacks.
- Access Control: Implementing strict access controls, including physical and digital barriers, can limit the ability of infiltrators to access sensitive areas or information.
- Monitoring and Surveillance: Regular monitoring of behavior and activities, especially in high-risk areas, can help detect infiltrators early.
Conclusion and Next Steps
In conclusion, recognizing and preventing infiltration is a critical task for ensuring the security and integrity of individuals, organizations, and communities. By understanding the signs and behaviors of infiltrators, and by implementing proactive protective measures, it's possible to significantly reduce the risk of infiltration. Continuous vigilance and education are key components of any security strategy, as the methods and tactics of infiltrators are constantly evolving.
Gallery of Infiltration Signs
Infiltration Signs Image Gallery







What are the most common signs of an infiltrator?
+The most common signs include unusual behavior, evasiveness, inconsistencies in their story or background, being overly curious, and technical issues that could indicate a cyber breach.
How can I protect my organization from infiltrators?
+Protection measures include conducting thorough background checks, providing security awareness training, implementing strict access controls, and regularly monitoring for suspicious activities.
What are the different types of infiltrators?
+Types of infiltrators include corporate spies, cyber hackers, terrorist infiltrators, and social engineers, each with different motivations and methods of operation.
We invite you to share your thoughts and experiences regarding the signs of infiltrators and how to protect against them. Your insights can help create a more secure and informed community. Whether you're an individual looking to safeguard your personal information or an organization seeking to protect its assets, understanding and addressing the issue of infiltration is a critical step forward. By working together and staying vigilant, we can reduce the risks associated with infiltrators and build safer, more secure environments for everyone.
