Intro
Boost military cyber security with MOS expertise, leveraging threat intelligence, network defense, and cybersecurity operations to protect against cyber threats and enhance national security.
The importance of military cyber security cannot be overstated in today's digital age. As technology continues to advance and play a larger role in modern warfare, the need for effective cyber security measures to protect military operations and assets has become a top priority. The Military Occupational Specialty (MOS) code for cyber security specialists is a critical component of this effort, as these individuals are responsible for defending against cyber threats and ensuring the integrity of military computer systems and networks.
The role of cyber security in the military is multifaceted and far-reaching. Not only must military cyber security specialists protect against external threats such as hacking and malware, but they must also ensure that military systems and networks are secure from internal threats, such as insider attacks and data breaches. This requires a deep understanding of computer systems, networks, and cyber security protocols, as well as the ability to stay up-to-date with the latest threats and vulnerabilities.
As the military continues to rely more heavily on technology, the demand for skilled cyber security specialists is likely to increase. This is why the Military Cyber Security MOS is such a vital part of the military's overall cyber security strategy. By recruiting and training highly skilled cyber security specialists, the military can ensure that its systems and networks are protected from cyber threats and that its operations can continue uninterrupted.
Military Cyber Security Threats

The types of cyber threats faced by the military are diverse and constantly evolving. Some of the most common threats include hacking, malware, phishing, and denial-of-service (DoS) attacks. These threats can come from a variety of sources, including foreign governments, terrorist organizations, and individual hackers. The military must also be aware of the threat posed by insider attacks, which can be particularly damaging due to the level of access and knowledge that insiders possess.
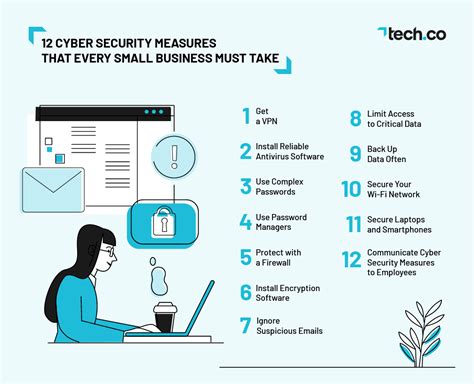
To combat these threats, the military uses a range of cyber security measures, including firewalls, intrusion detection systems, and encryption. The military also conducts regular security audits and risk assessments to identify vulnerabilities and implement corrective measures. Additionally, the military provides training and awareness programs to educate personnel on cyber security best practices and the importance of protecting sensitive information.
Cyber Security Measures

The military has implemented a range of cyber security measures to protect its systems and networks. These measures include the use of secure communication protocols, such as Secure Sockets Layer (SSL) and Transport Layer Security (TLS), to encrypt data in transit. The military also uses virtual private networks (VPNs) to secure remote access to its networks and systems.
In addition to these technical measures, the military has also implemented a range of operational security measures to protect its systems and networks. These measures include the use of secure passwords and authentication protocols, such as multi-factor authentication, to control access to sensitive systems and data. The military also conducts regular security audits and risk assessments to identify vulnerabilities and implement corrective measures.
Military Cyber Security Careers

There are a range of career paths available in military cyber security, from entry-level positions to senior leadership roles. Some of the most common career paths include cyber security specialist, incident responder, and security analyst. These roles involve a range of responsibilities, from monitoring systems and networks for security threats to responding to incidents and implementing corrective measures.
To pursue a career in military cyber security, individuals typically need to possess a range of skills and qualifications, including a strong understanding of computer systems and networks, as well as experience with cyber security protocols and technologies. The military also provides training and certification programs to help individuals develop the skills and knowledge they need to succeed in these roles.
Cyber Security Training and Certification

The military provides a range of training and certification programs to help individuals develop the skills and knowledge they need to succeed in cyber security roles. These programs include basic training courses, such as the Cyber Security Fundamentals course, as well as advanced training courses, such as the Cyber Security Advanced Course.
In addition to these training programs, the military also offers a range of certification programs, such as the Certified Information Systems Security Professional (CISSP) certification. These certifications demonstrate that an individual has the skills and knowledge required to perform specific cyber security tasks and responsibilities.
Military Cyber Security Operations

Military cyber security operations involve a range of activities, from monitoring systems and networks for security threats to responding to incidents and implementing corrective measures. These operations are typically carried out by specialized teams, such as the Cyber Security Operations Team, which is responsible for detecting and responding to cyber threats.
The military also conducts regular exercises and simulations to test its cyber security capabilities and identify areas for improvement. These exercises involve a range of scenarios, from responding to a cyber attack to conducting a cyber security audit.
Cyber Security and Intelligence

Cyber security and intelligence are closely linked, as cyber security threats often involve the use of intelligence gathering techniques, such as surveillance and reconnaissance. The military uses a range of intelligence gathering techniques to identify and track cyber threats, including signals intelligence and human intelligence.
The military also uses intelligence analysis to identify patterns and trends in cyber threats, and to anticipate and prepare for future threats. This involves analyzing data from a range of sources, including network logs and system alerts, to identify potential security vulnerabilities and threats.
Gallery of Military Cyber Security
Military Cyber Security Image Gallery









What is the role of cyber security in the military?
+The role of cyber security in the military is to protect military systems and networks from cyber threats and ensure the integrity of military operations.
What types of cyber threats does the military face?
+The military faces a range of cyber threats, including hacking, malware, phishing, and denial-of-service (DoS) attacks.
How does the military protect against cyber threats?
+The military uses a range of cyber security measures, including firewalls, intrusion detection systems, and encryption, to protect against cyber threats.
What is the Military Cyber Security MOS?
+The Military Cyber Security MOS is a critical component of the military's overall cyber security strategy, responsible for defending against cyber threats and ensuring the integrity of military computer systems and networks.
What career paths are available in military cyber security?
+There are a range of career paths available in military cyber security, from entry-level positions to senior leadership roles, including cyber security specialist, incident responder, and security analyst.
In conclusion, the importance of military cyber security cannot be overstated. As technology continues to play a larger role in modern warfare, the need for effective cyber security measures to protect military operations and assets has become a top priority. The Military Cyber Security MOS is a critical component of this effort, and individuals interested in pursuing a career in this field should possess a range of skills and qualifications, including a strong understanding of computer systems and networks, as well as experience with cyber security protocols and technologies. By staying informed and up-to-date on the latest cyber security threats and technologies, individuals can help protect the military's systems and networks and ensure the integrity of military operations. We invite you to share your thoughts and questions about military cyber security in the comments section below.
