Intro
Boost online security with 5 cyber tips, including phishing prevention, password management, and malware protection, to safeguard against cyber threats and ensure digital safety.
In today's digital age, cybersecurity is more important than ever. With the rise of technology and the internet, our personal and professional lives are increasingly dependent on digital platforms. However, this increased reliance on technology also brings with it a host of potential risks and threats. From identity theft to data breaches, the consequences of a cyber attack can be severe and long-lasting. Therefore, it is essential that we take steps to protect ourselves and our organizations from these threats.
The importance of cybersecurity cannot be overstated. A single cyber attack can result in significant financial losses, damage to reputation, and even legal action. Furthermore, the impact of a cyber attack can be felt for years to come, making it essential to take proactive measures to prevent such incidents from occurring in the first place. By following a few simple cyber tips, individuals and organizations can significantly reduce their risk of falling victim to a cyber attack.
Cybersecurity is not just a concern for large organizations; it is also a critical issue for individuals. With the rise of social media and online banking, our personal information is more vulnerable than ever. A single mistake, such as using a weak password or clicking on a phishing link, can result in significant consequences. Therefore, it is essential that individuals take steps to protect themselves and their personal information from cyber threats.
Cybersecurity Basics
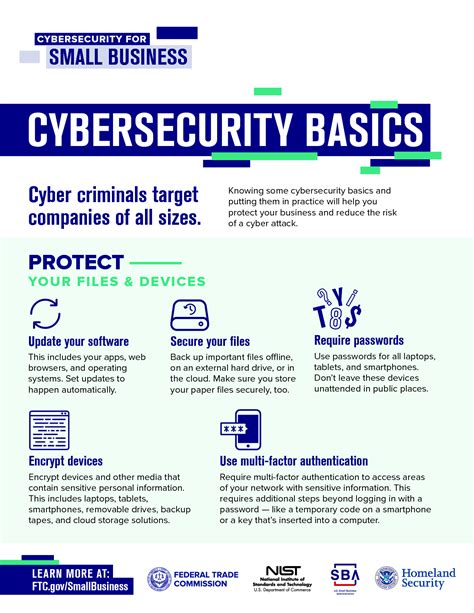
To protect ourselves from cyber threats, it is essential to understand the basics of cybersecurity. This includes using strong passwords, keeping software up to date, and being cautious when clicking on links or downloading attachments. Additionally, individuals and organizations should implement robust security measures, such as firewalls and antivirus software, to prevent cyber attacks. By following these simple steps, we can significantly reduce our risk of falling victim to a cyber attack.
Understanding Cyber Threats
Cyber threats come in many forms, including viruses, malware, and phishing attacks. Viruses are malicious programs that can damage or destroy data, while malware is software that is designed to harm or exploit a computer system. Phishing attacks, on the other hand, involve tricking individuals into revealing sensitive information, such as passwords or financial information. To protect ourselves from these threats, it is essential to understand how they work and how to prevent them.Cybersecurity Best Practices

To protect ourselves from cyber threats, it is essential to follow cybersecurity best practices. This includes using strong passwords, keeping software up to date, and being cautious when clicking on links or downloading attachments. Additionally, individuals and organizations should implement robust security measures, such as firewalls and antivirus software, to prevent cyber attacks. By following these simple steps, we can significantly reduce our risk of falling victim to a cyber attack.
Some of the key cybersecurity best practices include:
- Using strong, unique passwords for all accounts
- Keeping software and operating systems up to date
- Being cautious when clicking on links or downloading attachments
- Implementing robust security measures, such as firewalls and antivirus software
- Regularly backing up data to prevent losses in the event of a cyber attack
Implementing Cybersecurity Measures
Implementing cybersecurity measures is critical to protecting ourselves and our organizations from cyber threats. This includes implementing robust security measures, such as firewalls and antivirus software, as well as regularly updating software and operating systems. Additionally, individuals and organizations should use strong, unique passwords for all accounts and be cautious when clicking on links or downloading attachments.Cybersecurity Tools and Technologies
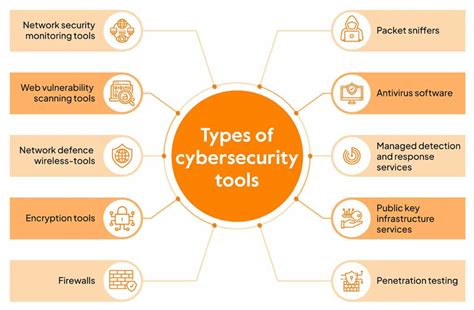
There are many cybersecurity tools and technologies available to help protect ourselves and our organizations from cyber threats. These include firewalls, antivirus software, and virtual private networks (VPNs). Firewalls help to block unauthorized access to computer systems, while antivirus software helps to detect and remove malware. VPNs, on the other hand, help to encrypt internet traffic, making it more difficult for hackers to intercept sensitive information.
Some of the key cybersecurity tools and technologies include:
- Firewalls: help to block unauthorized access to computer systems
- Antivirus software: helps to detect and remove malware
- Virtual private networks (VPNs): help to encrypt internet traffic
- Encryption software: helps to protect sensitive information by converting it into an unreadable code
- Intrusion detection systems: help to detect and alert individuals and organizations to potential cyber threats
Cybersecurity Awareness and Training
Cybersecurity awareness and training are critical to protecting ourselves and our organizations from cyber threats. This includes educating individuals on cybersecurity best practices, such as using strong passwords and being cautious when clicking on links or downloading attachments. Additionally, organizations should provide regular cybersecurity training to employees to help them understand the risks and consequences of cyber attacks.Cybersecurity Incident Response

In the event of a cyber attack, it is essential to have a plan in place to respond quickly and effectively. This includes identifying the source of the attack, containing the damage, and restoring systems and data. Additionally, individuals and organizations should have a plan in place to communicate with stakeholders, such as customers and employees, in the event of a cyber attack.
Some of the key steps in responding to a cyber attack include:
- Identifying the source of the attack
- Containing the damage
- Restoring systems and data
- Communicating with stakeholders
- Conducting a post-incident review to identify areas for improvement
Cybersecurity and Compliance
Cybersecurity and compliance are closely linked, as many industries are subject to regulations and laws related to cybersecurity. For example, the General Data Protection Regulation (GDPR) in the European Union requires organizations to implement robust cybersecurity measures to protect personal data. Additionally, the Payment Card Industry Data Security Standard (PCI DSS) requires organizations that handle credit card information to implement robust cybersecurity measures to protect sensitive information.Cybersecurity Trends and Predictions

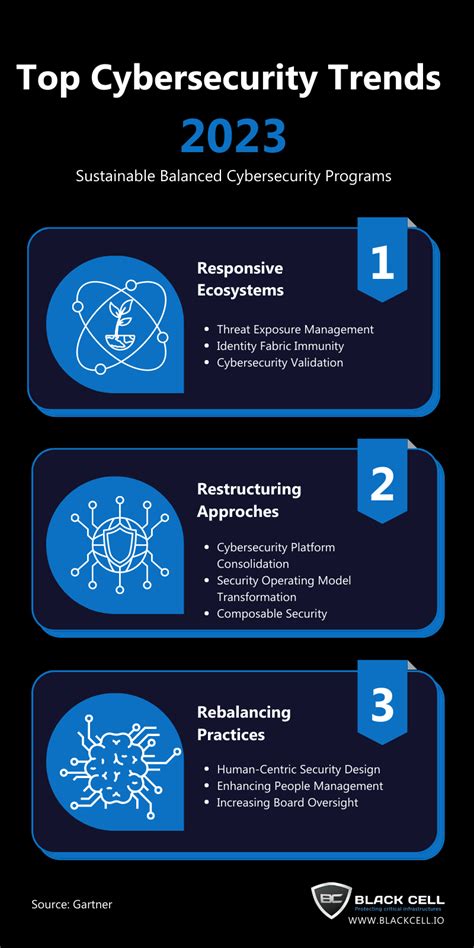
The cybersecurity landscape is constantly evolving, with new threats and technologies emerging all the time. Some of the key trends and predictions in cybersecurity include:
- Increased use of artificial intelligence and machine learning to detect and respond to cyber threats
- Greater emphasis on cloud security, as more organizations move their data and applications to the cloud
- Increased use of IoT devices, which can create new vulnerabilities and risks
- Greater emphasis on cybersecurity awareness and training, as individuals and organizations recognize the importance of cybersecurity
Cybersecurity and the Future
The future of cybersecurity is uncertain, but one thing is clear: cybersecurity will continue to be a critical issue for individuals and organizations. As technology continues to evolve, new threats and vulnerabilities will emerge, and it will be essential to stay ahead of the curve to protect ourselves and our organizations. By following cybersecurity best practices, implementing robust security measures, and staying informed about the latest trends and predictions, we can help to ensure a safe and secure digital future.Cybersecurity Image Gallery







What is cybersecurity?
+Cybersecurity refers to the practices, technologies, and processes designed to protect digital information, computer systems, and networks from unauthorized access, use, disclosure, disruption, modification, or destruction.
Why is cybersecurity important?
+Cybersecurity is important because it helps to protect sensitive information, prevent financial loss, and maintain the integrity of computer systems and networks.
What are some common cyber threats?
+Some common cyber threats include viruses, malware, phishing attacks, and denial-of-service attacks.
How can I protect myself from cyber threats?
+You can protect yourself from cyber threats by using strong passwords, keeping software up to date, being cautious when clicking on links or downloading attachments, and implementing robust security measures, such as firewalls and antivirus software.
What should I do in the event of a cyber attack?
+In the event of a cyber attack, you should identify the source of the attack, contain the damage, restore systems and data, communicate with stakeholders, and conduct a post-incident review to identify areas for improvement.
By following these cyber tips and staying informed about the latest trends and predictions, individuals and organizations can help to protect themselves from cyber threats and ensure a safe and secure digital future. Remember, cybersecurity is everyone's responsibility, and by working together, we can create a more secure and resilient digital world. If you have any questions or concerns about cybersecurity, please don't hesitate to reach out. Share this article with your friends and family to help spread awareness about the importance of cybersecurity. Together, we can make a difference and create a safer digital world for everyone.
