The world of cyber security is becoming increasingly complex, with new threats and challenges emerging every day. As technology advances, the difficulty level of cyber security is also escalating, making it harder for individuals and organizations to protect themselves from cyber attacks. In this article, we will explore the various aspects of cyber security difficulty level, its implications, and the measures that can be taken to mitigate these challenges.
The cyber security landscape is constantly evolving, with new vulnerabilities and threats being discovered regularly. The rise of advanced persistent threats (APTs), ransomware, and other sophisticated attacks has made it more difficult for security teams to detect and respond to incidents. Moreover, the increasing use of cloud computing, Internet of Things (IoT), and artificial intelligence (AI) has expanded the attack surface, providing more opportunities for hackers to exploit. The cyber security difficulty level is further compounded by the shortage of skilled cyber security professionals, making it challenging for organizations to find and retain talented individuals to manage their security operations.
Cyber Security Threats and Challenges
The cyber security difficulty level is influenced by various factors, including the type and sophistication of threats, the complexity of security systems, and the availability of resources and expertise. Some of the most significant cyber security threats and challenges include:
* Advanced persistent threats (APTs): These are sophisticated, targeted attacks that use multiple vectors to breach an organization's security.
* Ransomware: This type of malware encrypts an organization's data and demands payment in exchange for the decryption key.
* Phishing and social engineering: These attacks use psychological manipulation to trick individuals into divulging sensitive information or performing certain actions.
* IoT vulnerabilities: The increasing use of IoT devices has expanded the attack surface, providing more opportunities for hackers to exploit.
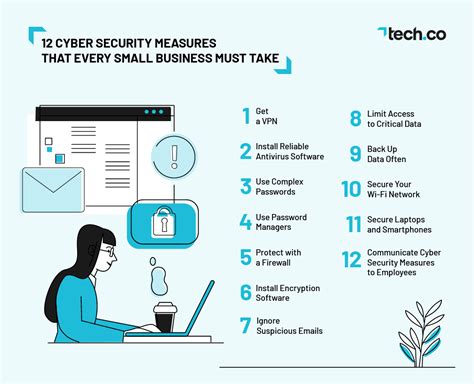
Cyber Security Measures and Best Practices
To mitigate the cyber security difficulty level, individuals and organizations can implement various measures and best practices, including:
* Implementing robust security controls, such as firewalls, intrusion detection systems, and antivirus software.
* Conducting regular security audits and penetration testing to identify vulnerabilities.
* Providing ongoing training and awareness programs for employees to educate them on cyber security best practices.
* Implementing incident response plans to quickly respond to and contain security incidents.
* Using encryption and secure communication protocols to protect sensitive data.
Cyber Security Frameworks and Standards
Cyber security frameworks and standards provide a structured approach to managing cyber security risks and improving the overall security posture of an organization. Some of the most widely used cyber security frameworks and standards include:
* NIST Cybersecurity Framework: This framework provides a comprehensive approach to managing cyber security risks, including identify, protect, detect, respond, and recover.
* ISO 27001: This standard provides a set of requirements for implementing an information security management system (ISMS).
* COBIT: This framework provides a set of best practices for IT governance and management, including cyber security.
Cyber Security Awareness and Training
Cyber security awareness and training are essential components of a comprehensive cyber security program. Individuals and organizations can benefit from ongoing training and awareness programs, including:
* Security awareness training: This type of training educates employees on cyber security best practices, including how to identify and report suspicious activity.
* Technical training: This type of training provides technical staff with the skills and knowledge needed to implement and manage security controls.
* Incident response training: This type of training prepares individuals to respond quickly and effectively to security incidents.
Cyber Security Incident Response
Cyber security incident response is critical to minimizing the impact of a security incident. A well-planned incident response plan should include:
* Incident detection: This involves identifying and detecting security incidents in a timely manner.
* Incident containment: This involves taking steps to prevent the incident from spreading and causing further damage.
* Incident eradication: This involves removing the root cause of the incident and restoring systems to a known good state.
* Incident recovery: This involves restoring systems and data to normal operation.
Cyber Security Governance and Compliance
Cyber security governance and compliance are critical components of a comprehensive cyber security program. Individuals and organizations must ensure that they are complying with relevant laws, regulations, and standards, including:
* Data protection regulations: These regulations, such as GDPR and HIPAA, require organizations to protect sensitive data and ensure its confidentiality, integrity, and availability.
* Industry standards: These standards, such as PCI-DSS and NIST, provide a set of requirements for implementing and managing security controls.
Cyber Security Risk Management
Cyber security risk management is the process of identifying, assessing, and mitigating cyber security risks. Individuals and organizations can benefit from implementing a risk management framework, including:
* Risk assessment: This involves identifying and assessing cyber security risks, including threats, vulnerabilities, and impacts.
* Risk mitigation: This involves implementing controls and countermeasures to mitigate identified risks.
* Risk monitoring: This involves continuously monitoring and reviewing the risk landscape to ensure that risks are being effectively managed.
Cyber Security Technologies and Tools
Cyber security technologies and tools are essential components of a comprehensive cyber security program. Individuals and organizations can benefit from implementing a range of technologies and tools, including:
* Firewalls: These devices control incoming and outgoing network traffic based on predetermined security rules.
* Intrusion detection systems: These systems monitor network traffic for signs of unauthorized access or malicious activity.
* Antivirus software: This software detects and removes malware from systems and devices.
Cyber Security Image Gallery
What is cyber security?
+
Cyber security refers to the practices, technologies, and processes designed to protect digital information, systems, and networks from unauthorized access, use, disclosure, disruption, modification, or destruction.
Why is cyber security important?
+
Cyber security is important because it helps protect sensitive information, systems, and networks from cyber threats, which can have significant financial, reputational, and operational consequences.
What are some common cyber security threats?
+
Some common cyber security threats include phishing, ransomware, malware, and denial-of-service (DoS) attacks.
How can I protect myself from cyber security threats?
+
You can protect yourself from cyber security threats by using strong passwords, keeping your software up to date, being cautious when clicking on links or opening attachments, and using antivirus software.
What is the difference between a virus and malware?
+
A virus is a type of malware that replicates itself by attaching to other programs or files, while malware is a broader term that refers to any type of malicious software, including viruses, Trojans, spyware, and adware.
In conclusion, the cyber security difficulty level is a complex and evolving challenge that requires a comprehensive approach to manage. By understanding the various aspects of cyber security, including threats, challenges, measures, and best practices, individuals and organizations can better protect themselves from cyber attacks. Remember to stay vigilant, keep your software up to date, and use strong passwords to minimize the risk of a security breach. Share this article with your friends and family to help spread awareness about the importance of cyber security, and don't hesitate to comment below if you have any questions or concerns.