Intro
Discover how military cybersecurity works through 5 key methods, utilizing threat intelligence, network security, and cyber warfare tactics to protect against cyber threats and attacks.
The importance of cybersecurity in the military cannot be overstated. As the world becomes increasingly dependent on technology, the risk of cyber threats to national security also grows. Military cybersecurity is a critical component of modern defense strategies, and its importance will only continue to increase in the coming years. In this article, we will delve into the world of military cybersecurity, exploring its key aspects, benefits, and the ways it works to protect military assets and personnel.
Cybersecurity is a broad term that encompasses a range of practices, technologies, and procedures designed to protect computer systems, networks, and sensitive information from unauthorized access, use, disclosure, disruption, modification, or destruction. In the military context, cybersecurity is crucial for ensuring the confidentiality, integrity, and availability of sensitive information, as well as the reliability and functionality of critical systems and infrastructure. The consequences of a cyber breach in the military can be severe, ranging from compromised operational security to loss of life.
The military faces a unique set of cybersecurity challenges, including the need to protect complex and diverse networks, systems, and devices, while also ensuring the security of sensitive information and maintaining operational effectiveness. To address these challenges, military organizations have developed a range of cybersecurity strategies and technologies, including threat detection and response systems, encryption and authentication protocols, and secure communication networks. By understanding how military cybersecurity works, we can better appreciate the importance of this critical component of modern defense and the ways it contributes to national security.
Introduction to Military Cybersecurity

Military cybersecurity is a complex and multifaceted field that involves the application of various technologies, practices, and procedures to protect military computer systems, networks, and sensitive information from cyber threats. The military relies heavily on computer systems and networks to perform a range of critical functions, including command and control, communications, intelligence, surveillance, and reconnaissance. These systems and networks are vulnerable to cyber threats, which can compromise their confidentiality, integrity, and availability.
Key Aspects of Military Cybersecurity
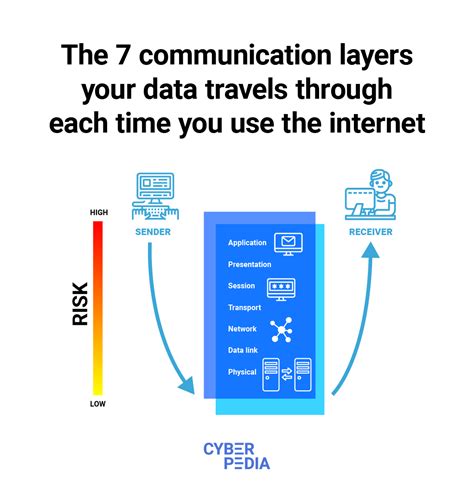
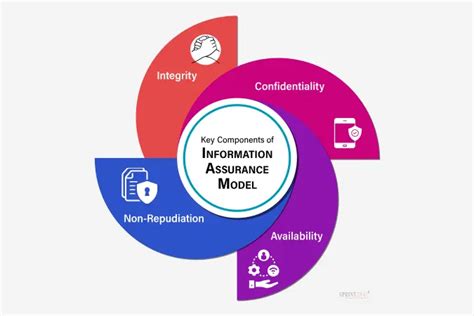
The key aspects of military cybersecurity include threat detection and response, network security, cryptography, secure communication protocols, and information assurance. Threat detection and response involve the use of various technologies and techniques to identify and respond to cyber threats in real-time. Network security involves the implementation of various measures to protect military networks from unauthorized access, use, disclosure, disruption, modification, or destruction. Cryptography involves the use of encryption and decryption techniques to protect sensitive information from unauthorized access. Secure communication protocols involve the use of secure communication networks and protocols to protect sensitive information from interception or eavesdropping. Information assurance involves the implementation of various measures to ensure the confidentiality, integrity, and availability of sensitive information.5 Ways Military Cybersecurity Works

Military cybersecurity works in a variety of ways to protect military assets and personnel from cyber threats. Here are five ways military cybersecurity works:
- Threat Detection and Response: The military uses various technologies and techniques to detect and respond to cyber threats in real-time. This includes the use of intrusion detection systems, firewalls, and antivirus software to identify and block malicious traffic. The military also uses threat intelligence to anticipate and prepare for potential cyber threats.
- Network Security: The military implements various measures to protect its networks from unauthorized access, use, disclosure, disruption, modification, or destruction. This includes the use of firewalls, intrusion detection systems, and encryption to protect sensitive information from unauthorized access.
- Cryptography: The military uses cryptography to protect sensitive information from unauthorized access. This includes the use of encryption and decryption techniques to protect sensitive information from interception or eavesdropping.
- Secure Communication Protocols: The military uses secure communication protocols to protect sensitive information from interception or eavesdropping. This includes the use of secure communication networks and protocols, such as satellite communications and secure radio protocols.
- Information Assurance: The military implements various measures to ensure the confidentiality, integrity, and availability of sensitive information. This includes the use of access controls, authentication protocols, and encryption to protect sensitive information from unauthorized access.
Benefits of Military Cybersecurity
The benefits of military cybersecurity are numerous and significant. These benefits include:- Protection of Sensitive Information: Military cybersecurity protects sensitive information from unauthorized access, use, disclosure, disruption, modification, or destruction.
- Prevention of Cyber Attacks: Military cybersecurity prevents cyber attacks from compromising military networks and systems.
- Ensuring Operational Effectiveness: Military cybersecurity ensures the operational effectiveness of military systems and networks.
- Protection of Personnel: Military cybersecurity protects military personnel from cyber threats that could compromise their safety and security.
- Enhancing National Security: Military cybersecurity enhances national security by protecting military assets and personnel from cyber threats.
Challenges Facing Military Cybersecurity

Despite the importance of military cybersecurity, there are several challenges facing this critical component of modern defense. These challenges include:
- Complexity of Military Networks: Military networks are complex and diverse, making it challenging to implement effective cybersecurity measures.
- Evolution of Cyber Threats: Cyber threats are evolving rapidly, making it challenging for military cybersecurity to keep pace.
- Limited Resources: Military cybersecurity often has limited resources, including budget and personnel, making it challenging to implement effective cybersecurity measures.
- Balancing Security and Operational Effectiveness: Military cybersecurity must balance security with operational effectiveness, making it challenging to implement effective cybersecurity measures without compromising military operations.
Future of Military Cybersecurity
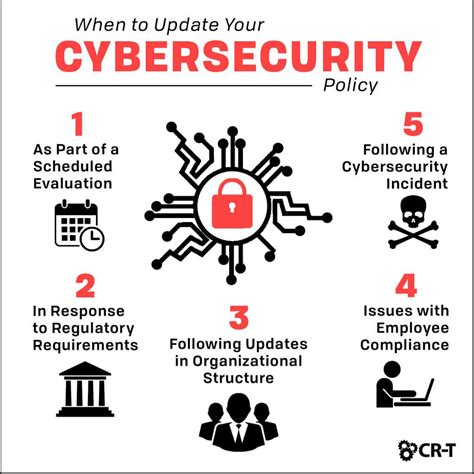
The future of military cybersecurity is uncertain, but it is clear that this critical component of modern defense will continue to play a vital role in protecting military assets and personnel from cyber threats. The military will need to continue to evolve and adapt its cybersecurity measures to keep pace with the evolving cyber threat landscape. This will require significant investment in cybersecurity technologies, personnel, and training, as well as a commitment to ongoing research and development.Gallery of Military Cybersecurity Images
Military Cybersecurity Image Gallery






Frequently Asked Questions
What is military cybersecurity?
+Military cybersecurity refers to the practices, technologies, and procedures used to protect military computer systems, networks, and sensitive information from cyber threats.
Why is military cybersecurity important?
+Military cybersecurity is important because it protects military assets and personnel from cyber threats that could compromise their safety and security, as well as the operational effectiveness of military systems and networks.
What are some common cyber threats faced by the military?
+Some common cyber threats faced by the military include malware, phishing, denial-of-service attacks, and advanced persistent threats.
How does the military protect itself from cyber threats?
+The military protects itself from cyber threats through a range of measures, including threat detection and response, network security, cryptography, secure communication protocols, and information assurance.
What is the future of military cybersecurity?
+The future of military cybersecurity will involve the continued evolution and adaptation of cybersecurity measures to keep pace with the evolving cyber threat landscape, as well as significant investment in cybersecurity technologies, personnel, and training.
In conclusion, military cybersecurity is a critical component of modern defense that plays a vital role in protecting military assets and personnel from cyber threats. By understanding how military cybersecurity works, we can better appreciate the importance of this critical component of national security. We encourage readers to share their thoughts and experiences on military cybersecurity in the comments section below, and to explore the various resources and references provided throughout this article to learn more about this important topic.
